Access requestor
Manager
Business sponsor
System owner
IT administrator
Security reviewer
Compliance reviewer
This process is used when an individual requires new, changed, or temporary access to internal systems, applications, or data. It commonly occurs during employee onboarding, role changes, project-based access needs, or periodic access reviews. The process becomes critical when access involves sensitive data, regulated systems, or multiple approval authorities across IT, security, and business teams.
Access approval typically involves the person requesting access, their manager or business sponsor, system owners responsible for the requested tools, IT administrators who provision access, and security or compliance reviewers who assess risk and policy alignment. In some organizations, audit or risk teams may also participate in oversight or review.
Reduced cycle time for approving and provisioning accessAppropriate access granted efficiently ensures users receive the access they need without unnecessary delays while maintaining security controls. Clear accountability for every access decision provides documented evidence of who authorized access and why. Reduced security exposure results from consistent evaluation of access requests against policy before provisioning. Improved audit readiness comes from complete records of access requests, approvals, and provisioning actions. Balanced security and productivity follows from approval processes that protect the organization without creating operational friction.
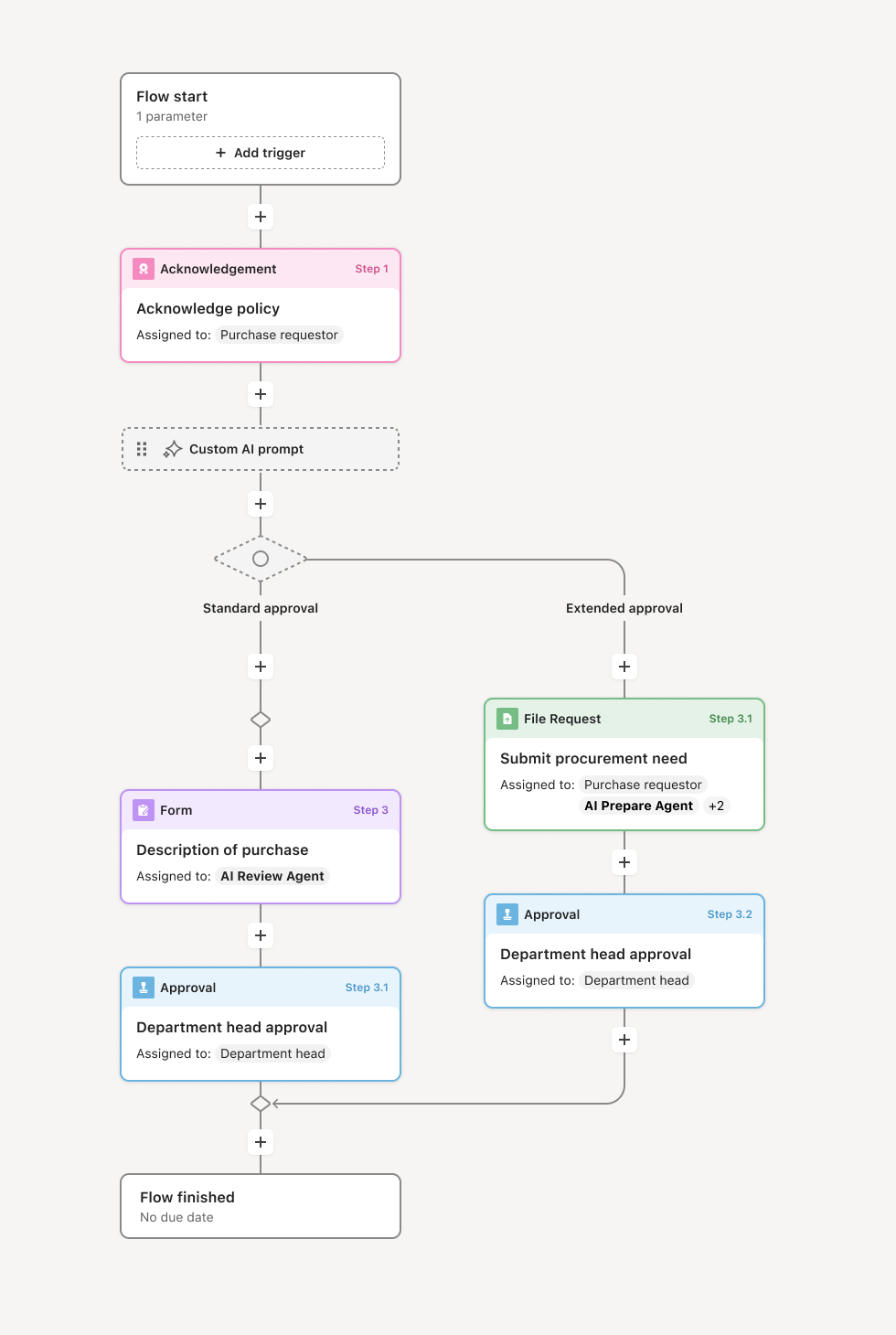
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo's flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Request initiation
The process begins when access is requested, either by an individual needing access or a manager requesting on behalf of a team member. The request specifies what access is needed, why it is required, and the duration if temporary. Supporting information such as project assignment, role documentation, or business case may be attached. An AI agent may assist by validating completeness and suggesting appropriate access levels based on role.
Business justification review
The requester's manager or sponsor validates that the access supports legitimate business needs and is appropriate for the individual's role. If the access seems excessive or misaligned with job function, the manager may modify the request or require additional justification. This step confirms organizational support for the access before technical evaluation.
Resource owner authorization
Owners of the specific systems, data, or facilities being accessed review and authorize the request. Owners evaluate whether granting access aligns with usage policies, whether prerequisites are met, and whether any conditions should apply. For shared resources, multiple owners may need to approve. If concerns exist, the workflow routes for clarification or modification.
Security and policy evaluation
Security teams evaluate access requests against organizational security policy. This includes checking for privilege accumulation, segregation of duties conflicts, and alignment with least-privilege principles. For access to sensitive resources, additional controls such as enhanced authentication or monitoring may be required as conditions of approval. Compliance reviews requests touching regulated data or systems.
Approval decision and conditions
Based on the reviews, the workflow captures the approval decision. Approvals may be unconditional or may include requirements such as time limitations, additional training, or enhanced monitoring. Rejections include rationale and guidance for the requester. All decisions are documented with full context.
Provisioning and acknowledgment
Upon approval, access is provisioned through appropriate channels. The requester receives confirmation and any required acknowledgments such as acceptable use policies. Provisioning may trigger automatically through connected systems or require manual action for certain resources. The access grant is recorded with effective dates and any conditions.
Lifecycle management
Access grants are tracked throughout their lifecycle. Temporary access expires automatically. Periodic recertification validates continued appropriateness. Changes in role or employment status trigger access review. Revocation processes remove access that is no longer appropriate. The complete access history supports audit and compliance requirements.
This process commonly relies on inputs such as access request details, role and job function information, resource catalogs, security policies, and compliance requirements. It may be triggered by onboarding processes, role changes, project assignments, or direct requests. Supporting systems often include identity and access management platforms, physical access control systems, HR systems, and resource-specific administration tools.
Key decision points include determining whether business justification supports the request, whether the access level is appropriate for the individual's role, whether security or compliance concerns require additional controls, and whether access should be time-limited or subject to recertification.
Access granted without proper authorization, bypassing required approvals. Business justification not validated, granting access without confirmed need. Security evaluation skipped for sensitive access, missing policy violations or conflicts. Access conditions not enforced, rendering approval controls ineffective. Lifecycle management neglected, allowing access to persist after it is no longer appropriate.
Orchestrates access approval across requesters, managers, resource owners, and security teams ensuring all required validations occur before access is granted.
Routes requests through appropriate approval paths based on resource sensitivity using conditional logic that enforces organizational policy.
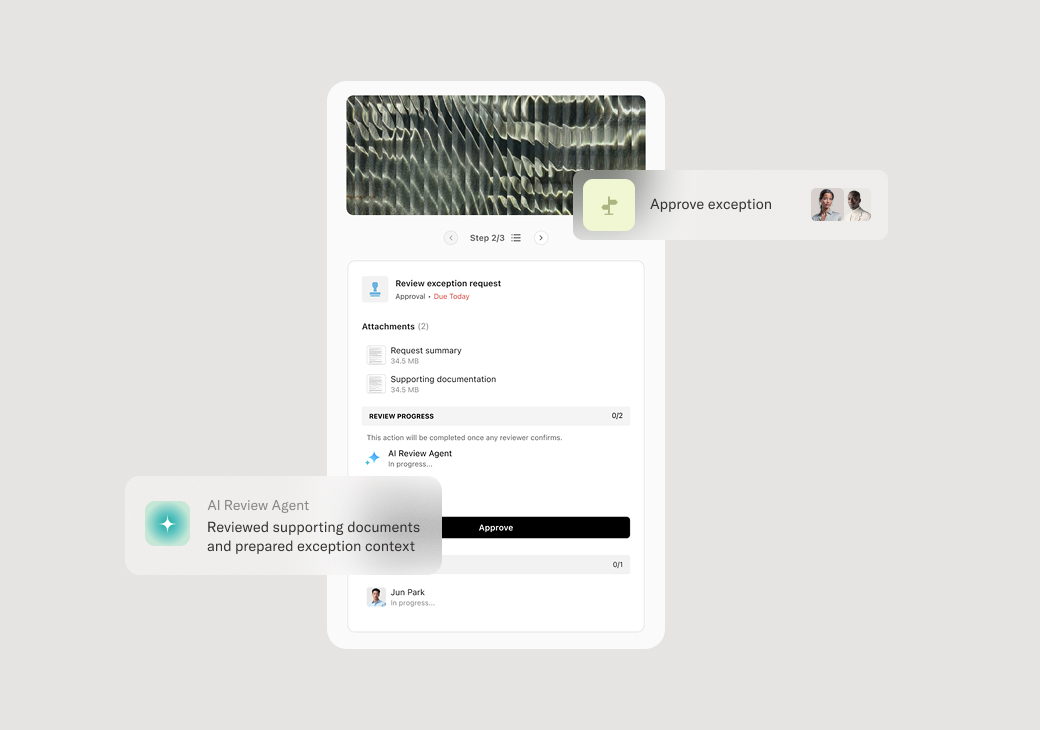
AI agents validate request completeness and flag potential security concerns helping catch issues before approval decisions are made.
Supports conditional approvals with tracked requirements such as time limits, training completion, or enhanced monitoring.
Maintains complete access lifecycle records from initial request through provisioning, recertification, and revocation.
Connects to identity and access management systems to automate provisioning and ensure consistent enforcement of approved access.