Requester
Manager
IT administrator
Security reviewer
Compliance reviewer

This process is used when individuals require new, modified, or temporary access to internal systems, applications, or sensitive data. It becomes especially important when access involves elevated permissions, regulated information, or multiple systems owned by different teams. Organizations rely on this process when coordination is required across managers, IT, security, and compliance to balance speed with risk control.
Access request approval commonly involves a requester who needs access, a manager who confirms business justification, IT administrators who provision access, and security or compliance reviewers who assess risk and policy alignment. In some organizations, system owners or auditors may also be involved depending on the sensitivity of the access.
Reduced cycle time for approving and provisioning access without bypassing controls
Clear ownership for access decisions and accountability
Improved visibility into who has access, why it was granted, and when it was approved
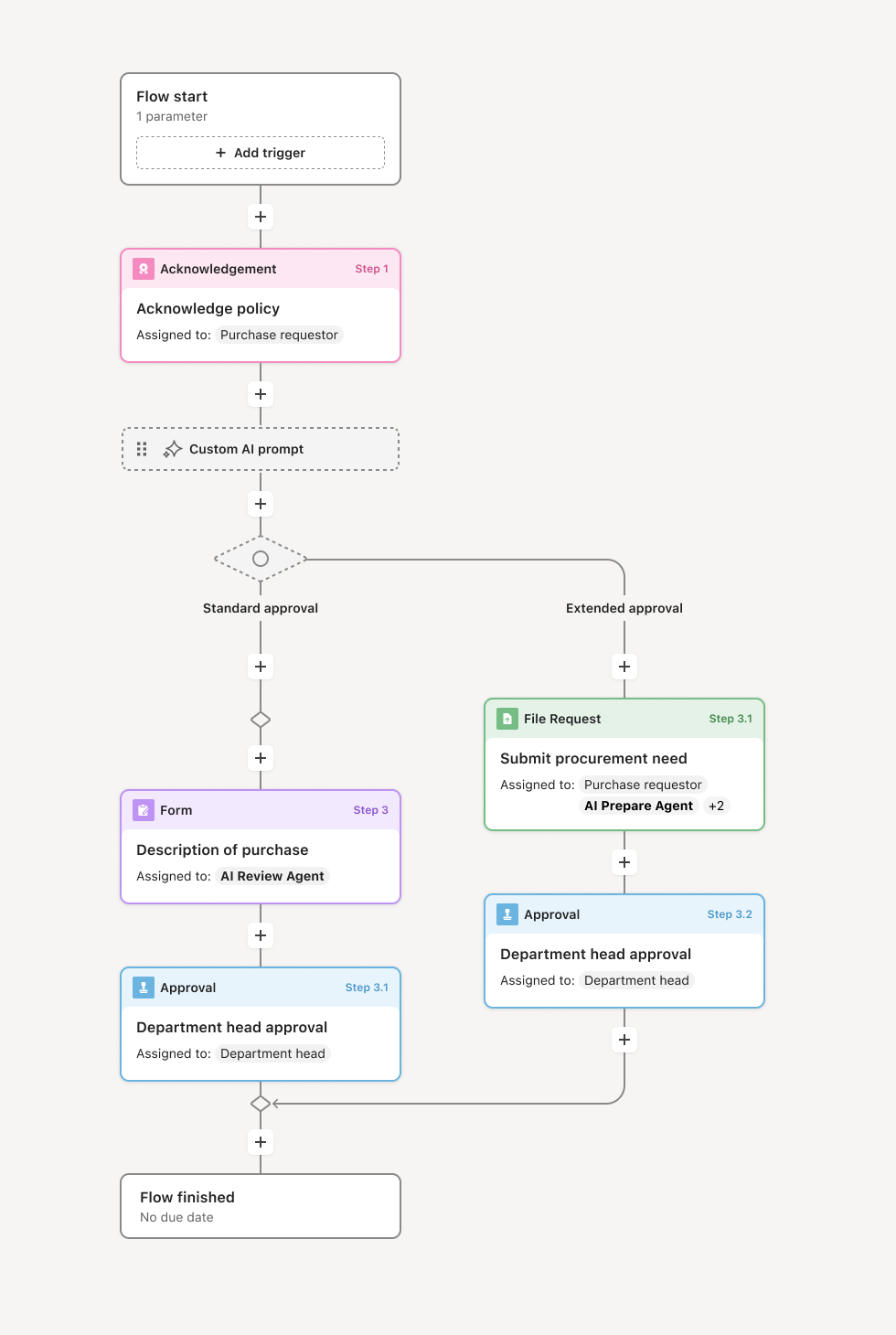
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo's flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Access request submission
The process begins when a user or their manager submits an access request, specifying the system, application, or resource needed, the level of access required, and the business justification. The request may be for a single system or bundled as a role-based access package. An AI agent may assist by suggesting access based on role, validating request completeness, and flagging potential conflicts.
Manager approval and business validation
The requester's manager reviews and approves the request, confirming the access is necessary for the employee's job function and aligns with their role. If the manager has concerns about the request or identifies excessive access, they may modify or reject it. Manager approval validates the business need before technical review.
System owner authorization
System or application owners review access requests for their platforms. Owners evaluate whether the requested access level is appropriate, whether the requester meets prerequisites, and whether granting access aligns with system usage policies. For sensitive systems, owners may require additional justification or impose conditions on access.
Security and compliance review
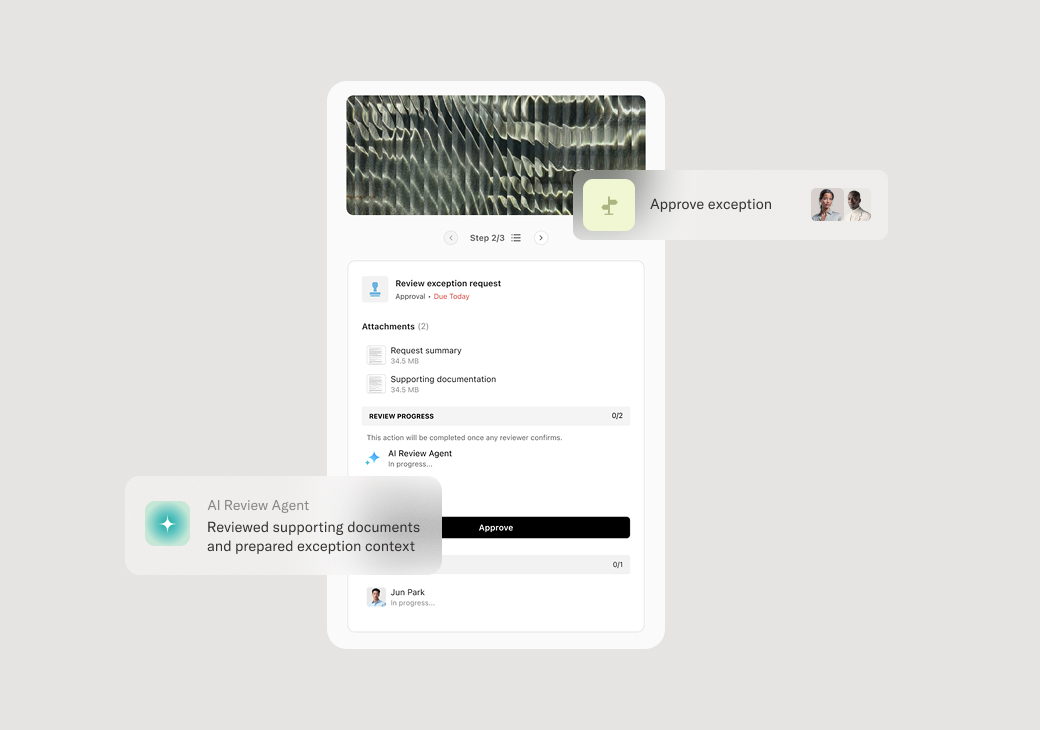
For access to sensitive data, critical systems, or resources with compliance implications, security and compliance teams evaluate the request. Security checks for segregation of duties conflicts, excessive privilege accumulation, and alignment with least-privilege principles. Compliance confirms access aligns with regulatory requirements. If issues are identified, the workflow routes for resolution before proceeding.
Provisioning and confirmation
Upon approval, the workflow triggers access provisioning. Credentials, permissions, or physical access are configured in the relevant systems. The requester receives confirmation of access grant along with any usage guidelines or acknowledgments required. Provisioning may be automatic through connected identity systems or manual for systems without integration.
Periodic review and recertification
Access grants are tracked for periodic review. Managers and system owners recertify that access remains appropriate. Access no longer needed is revoked through connected workflows. The complete history of access grants, recertifications, and revocations is retained for audit purposes.
This process commonly relies on inputs such as access request forms, organizational charts, role definitions, system catalogs, and compliance requirements. It may be triggered by employee onboarding, role change, project assignment, or direct request. Supporting systems often include identity and access management platforms, HR systems like Workday, Active Directory, and application-specific access control systems.
Key decision points include determining whether the business justification supports the access request, whether the access level is appropriate for the requester's role, whether security or compliance review is required, and whether access conflicts with segregation of duties requirements.
Access granted without manager validation, bypassing business need confirmation. System owners not involved in authorization, allowing access without platform-specific review. Segregation of duties conflicts not detected, creating control weaknesses. Access provisioning delayed, impacting employee productivity. Access never revoked when no longer needed, creating accumulated access risk.
Orchestrates access approval across managers, system owners, and security teams in a coordinated process that validates both business need and technical appropriateness.
Routes requests through appropriate approval paths based on system sensitivity and access level using conditional logic that enforces security policy.
AI agents suggest role-appropriate access and flag potential conflicts helping catch issues before access is granted.
Captures complete approval history documenting who authorized access, the business justification, and any conditions.
Tracks access lifecycle including grants, recertifications, and revocations for complete access governance.
Connects to identity management systems to trigger provisioning automatically upon approval.