IT security manager
Data governance lead
Identity access manager
Compliance officer
Information security analyst
IT operations director

When employees need access to systems or data for their roles. When access levels change due to role changes or project needs. When temporary access is required for specific initiatives. When access requests involve sensitive or regulated data. Ideal for enterprises, regulated industries, and any organization with data governance requirements.
Requesters submit access requests with business justification. Managers approve that the access is appropriate for the role. Data owners authorize access to their data domains. Security teams review compliance with access policies. IT provisions approved access in systems.
Appropriate access provisioning aligned with roles and business needs Compliant access management meeting regulatory and policy requirements Reduced unauthorized access risk through structured approval process Clear access audit trail documenting all access decisions
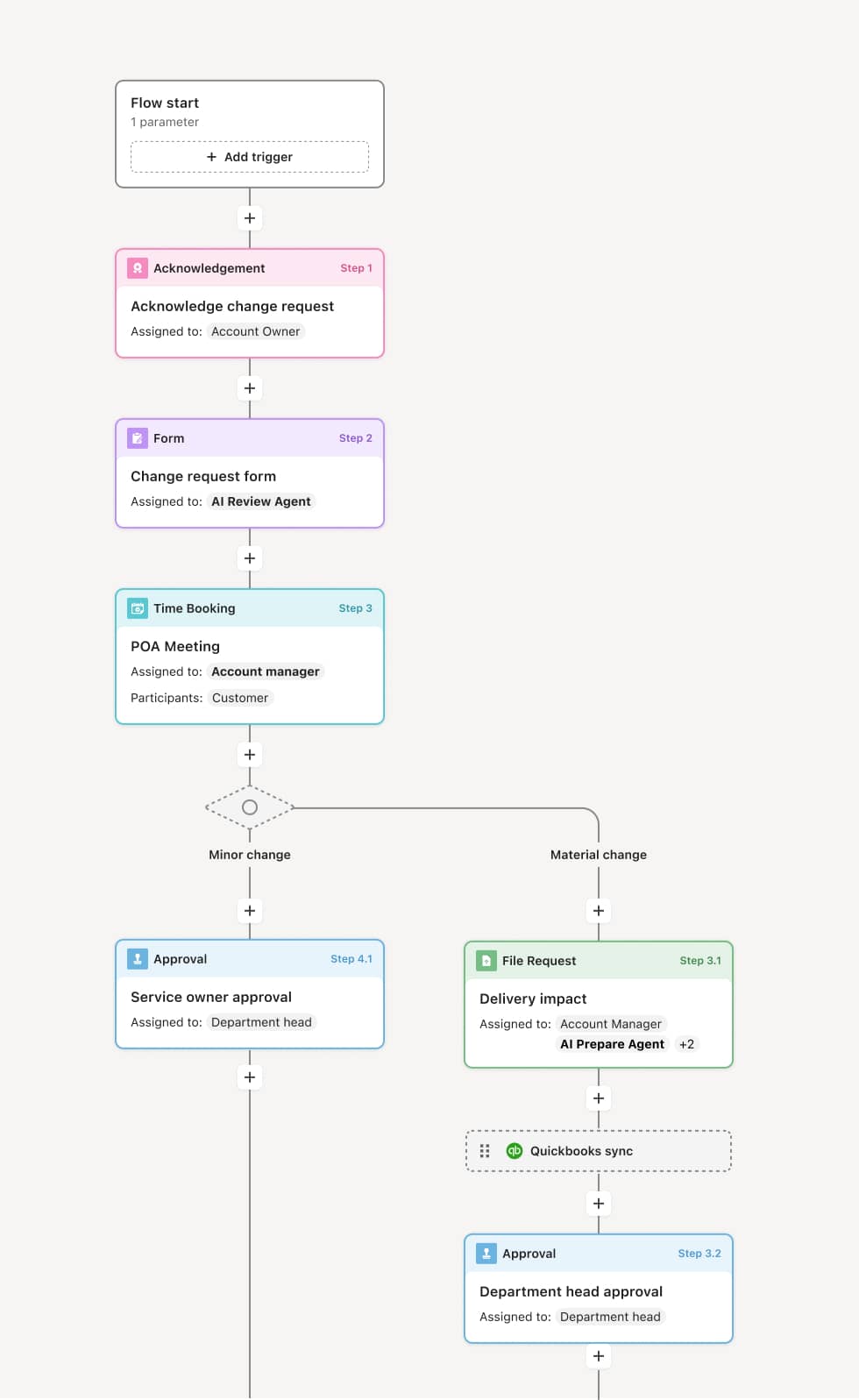
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo's flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Access request submission
The process begins when a user submits an access request specifying the system, data, or resource needed and the business justification. AI agents may validate the request against existing access and flag potential conflicts or excessive permissions.
Manager approval
The requester's manager reviews the request to confirm the access is appropriate for the role and job responsibilities. They may approve, deny, or request modification of the access scope.
Data owner authorization
For access to specific data domains, the data owner reviews the request. They evaluate whether the business need justifies the access and whether any restrictions should apply. Sensitive data may require additional justification.
Security and compliance review
Security teams review the request against access policies, segregation of duties requirements, and compliance obligations. They approve compliant requests or flag issues requiring resolution.
Provisioning and notification
Approved access is provisioned in the relevant systems. The requester is notified of their new access. Access expiration is set if temporary. The complete approval chain is logged for audit purposes.
This process relies on access requests, role definitions, access policies, and existing entitlement data. Triggers include new employee onboarding, role changes, project assignments, or direct requests. Integration with identity management platforms like Okta or Azure AD, HR systems like Workday, and access governance tools supports efficient processing.
Key decision points include determining whether the access is appropriate for the role, whether it creates segregation of duties conflicts, and whether compliance requirements are satisfied.
Access granted without proper justification creating security risk. Segregation of duties violations not detected. Access not removed when no longer needed. Approval delays impacting employee productivity.
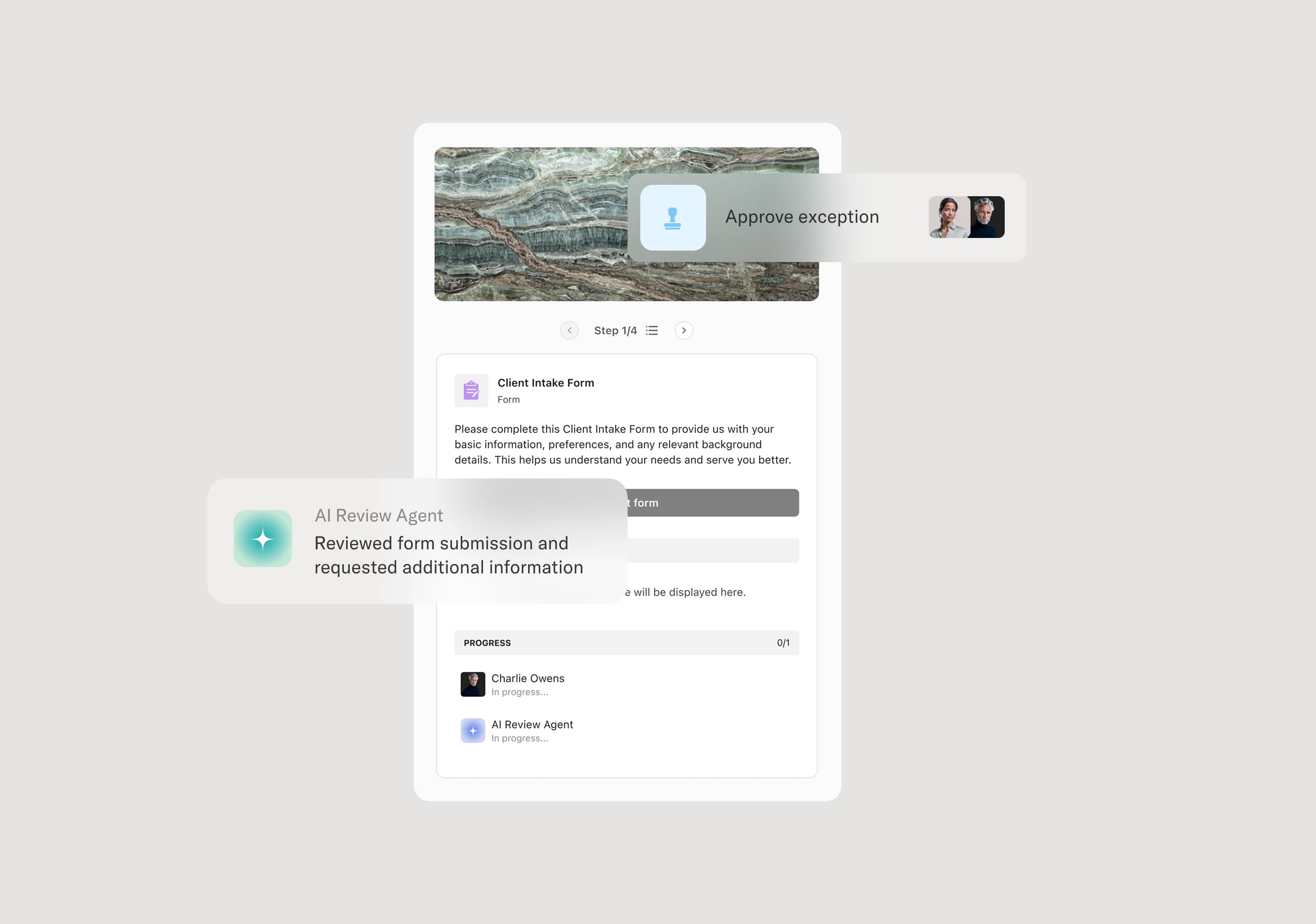
Orchestrates multi-level access approval across managers, data owners, and security
AI agents validate requests against existing access and flag potential conflicts
Integrates with identity management systems for automated provisioning
Maintains complete audit trail of all access decisions for compliance