Privacy officer
Legal counsel
Chief information security officer
Compliance manager
Vendor management lead
Data protection officer
When engaging vendors who will process personal data. When existing DPAs require renewal or amendment. When data processing activities change, requiring agreement updates. When regulatory requirements mandate specific DPA provisions. Ideal for organizations subject to GDPR, CCPA, or other privacy regulations, and any company sharing personal data with third parties.
Business teams identify data processing needs. Procurement or vendor management initiates agreements. Legal drafts or reviews DPA terms. Privacy teams ensure compliance with regulations. Security reviews data protection provisions. Executives authorize agreements with significant risk.
Privacy-compliant vendor relationships with appropriate data processing terms Reduced regulatory risk through standardized DPA requirements Clear processing boundaries documented for all third-party data handlers Efficient DPA negotiation through structured review and approval
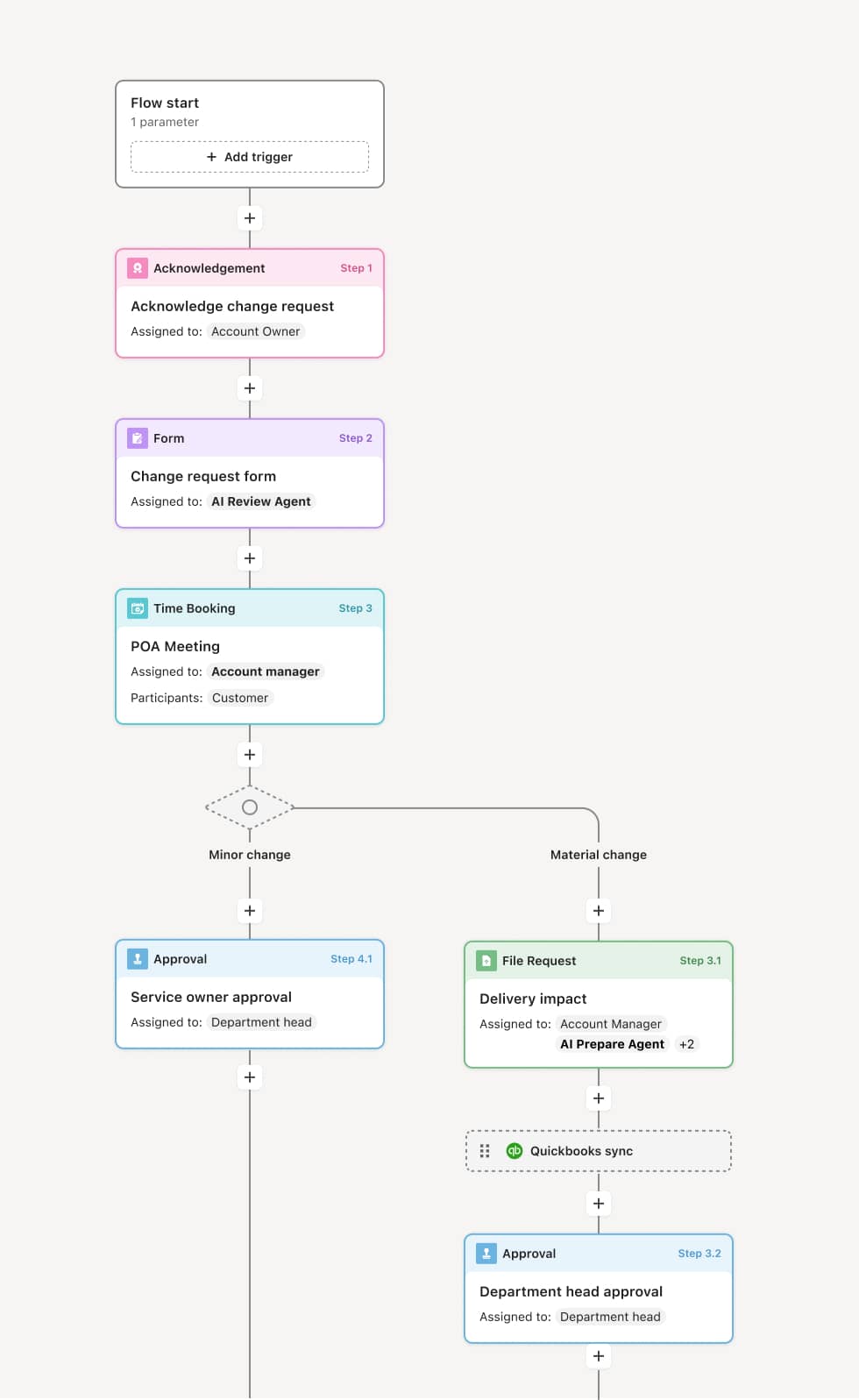
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo's flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
DPA initiation
The process begins when a vendor relationship requires a data processing agreement. Business teams submit details about the data to be processed, processing purposes, and vendor information. AI agents may identify applicable regulatory requirements based on data types and jurisdictions.
Legal review
Legal reviews the proposed DPA against standard terms and regulatory requirements. They identify gaps, negotiate amendments, and ensure adequate data subject rights protections. Redline versions are tracked through negotiation cycles.
Privacy and security review
Privacy teams review data handling provisions for compliance with regulations like GDPR or CCPA. Security reviews technical and organizational measures, breach notification terms, and audit rights. Issues are flagged for resolution.
Risk assessment
If the processing involves high-risk data or activities, a risk assessment is conducted. The assessment documents residual risks and any required mitigations. Unacceptable risks may require additional safeguards or prohibit the arrangement.
Authorization and execution
Approved DPAs are authorized for execution. Signatories are coordinated and signatures obtained. The executed agreement is stored with processing records. Expiration and renewal tracking is initiated.
This process relies on processing specifications, vendor information, DPA templates, and regulatory requirements. Triggers include new vendor engagements, renewal dates, or processing changes. Integration with contract management systems, vendor management platforms, and privacy management tools like OneTrust supports efficient governance.
Key decision points include determining whether the DPA provides adequate protections, whether residual risks are acceptable, and whether the processing arrangement aligns with regulatory requirements.
Processing initiated without executed DPA creating compliance exposure. Standard terms not applied consistently across vendors. DPA expiration missed leaving processing unprotected. Vendor processing changes not reflected in agreement amendments.
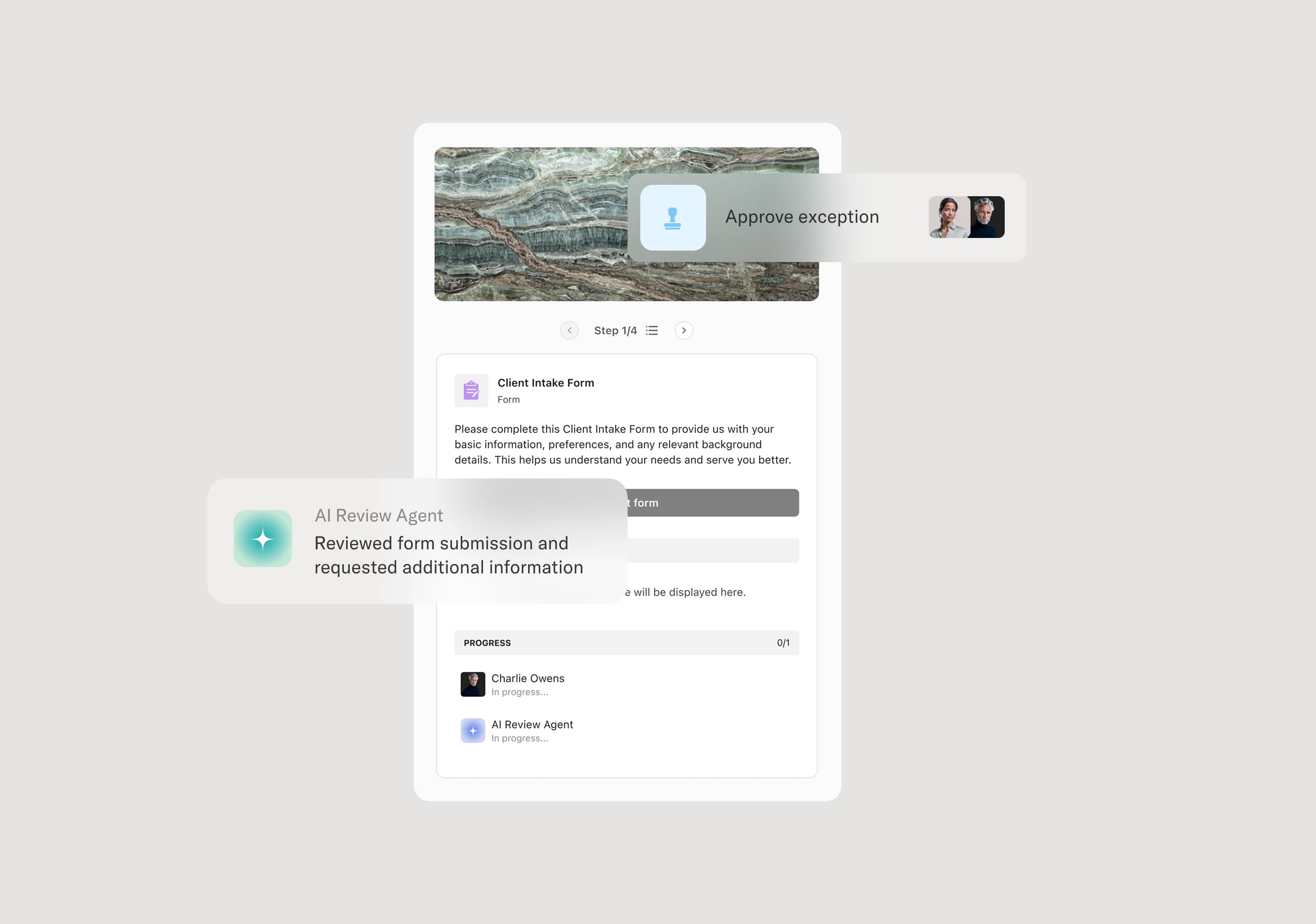
Orchestrates DPA review across legal, privacy, and security with coordinated negotiation tracking
AI agents identify applicable regulatory requirements and flag missing provisions
Coordinates multi-party authorization and signature collection
Tracks agreement expiration and processing changes requiring amendments