Data governance lead
Chief data officer
Privacy officer
Information security manager
Business intelligence director
Compliance officer

When business partners request access to organizational data. When internal teams need to share data across departmental boundaries. When data must be transferred to third-party platforms or analytics providers. When regulatory requirements govern data transfers. Ideal for data-driven organizations, companies with partner ecosystems, and any business sharing sensitive information.
Requesters submit data sharing requests with business justification. Data owners evaluate whether sharing is appropriate for their data domains. Security teams assess transfer mechanisms and recipient safeguards. Legal reviews contractual and regulatory requirements. Governance teams ensure policy compliance and maintain sharing records.
Controlled data distribution with clear authorization for each sharing arrangement Protected sensitive information through structured evaluation before sharing Compliant data transfers meeting regulatory and contractual requirements Auditable sharing history documenting what was shared, with whom, and why
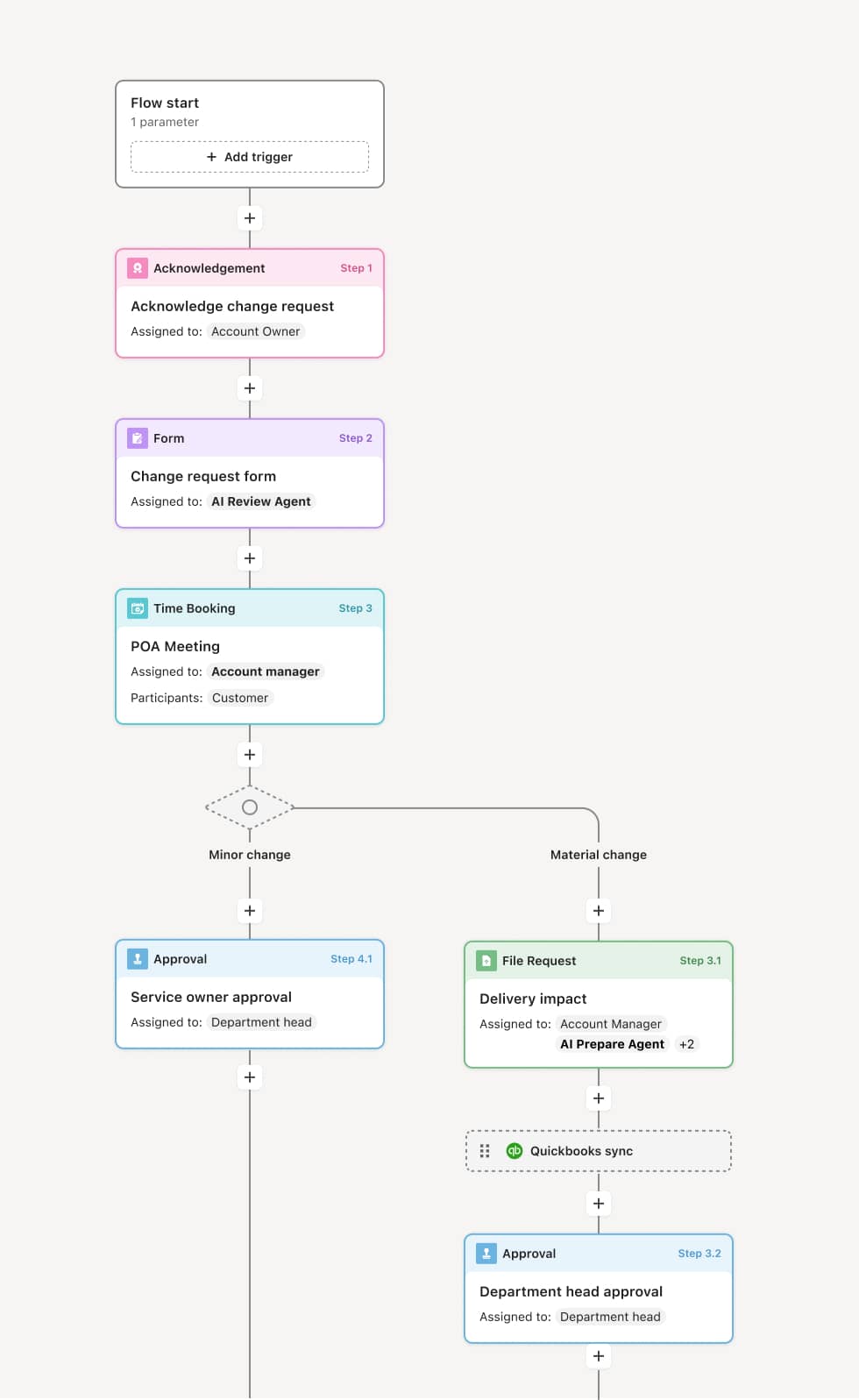
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo's flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Sharing request submission
The process begins when a data sharing request is submitted specifying the data sets, recipient, purpose, transfer method, and retention requirements. AI agents may classify the data sensitivity and identify applicable policies automatically.
Data owner review
The owner of the requested data evaluates whether sharing aligns with the data's intended use and whether the recipient and purpose are appropriate. They may approve, deny, or request modifications to the sharing scope.
Security and privacy assessment
Security teams evaluate the transfer mechanism, recipient security posture, and any encryption or anonymization requirements. Privacy teams assess regulatory implications, consent requirements, and cross-border transfer restrictions.
Legal and contractual review
For external sharing, legal reviews existing agreements, data sharing terms, and any required contracts. If agreements are not in place, the workflow may trigger contract negotiation before sharing can proceed.
Authorization and execution
Approved sharing requests are authorized with specific scope and conditions documented. The data transfer is executed according to approved parameters. Sharing records are maintained for audit and future reference.
This process relies on data catalogs, classification metadata, sharing agreements, and recipient information. Triggers include partner requests, internal project needs, or integration requirements. Integration with data governance platforms, master data management systems, and security tools supports controlled sharing.
Key decision points include determining whether the sharing purpose is legitimate, whether the recipient has adequate safeguards, whether regulatory requirements permit the transfer, and what conditions should govern the sharing.
Data shared without proper authorization creating compliance risk. Sensitive data transferred through insecure channels. Sharing scope creep beyond originally approved parameters. No record of what was shared making audit impossible.
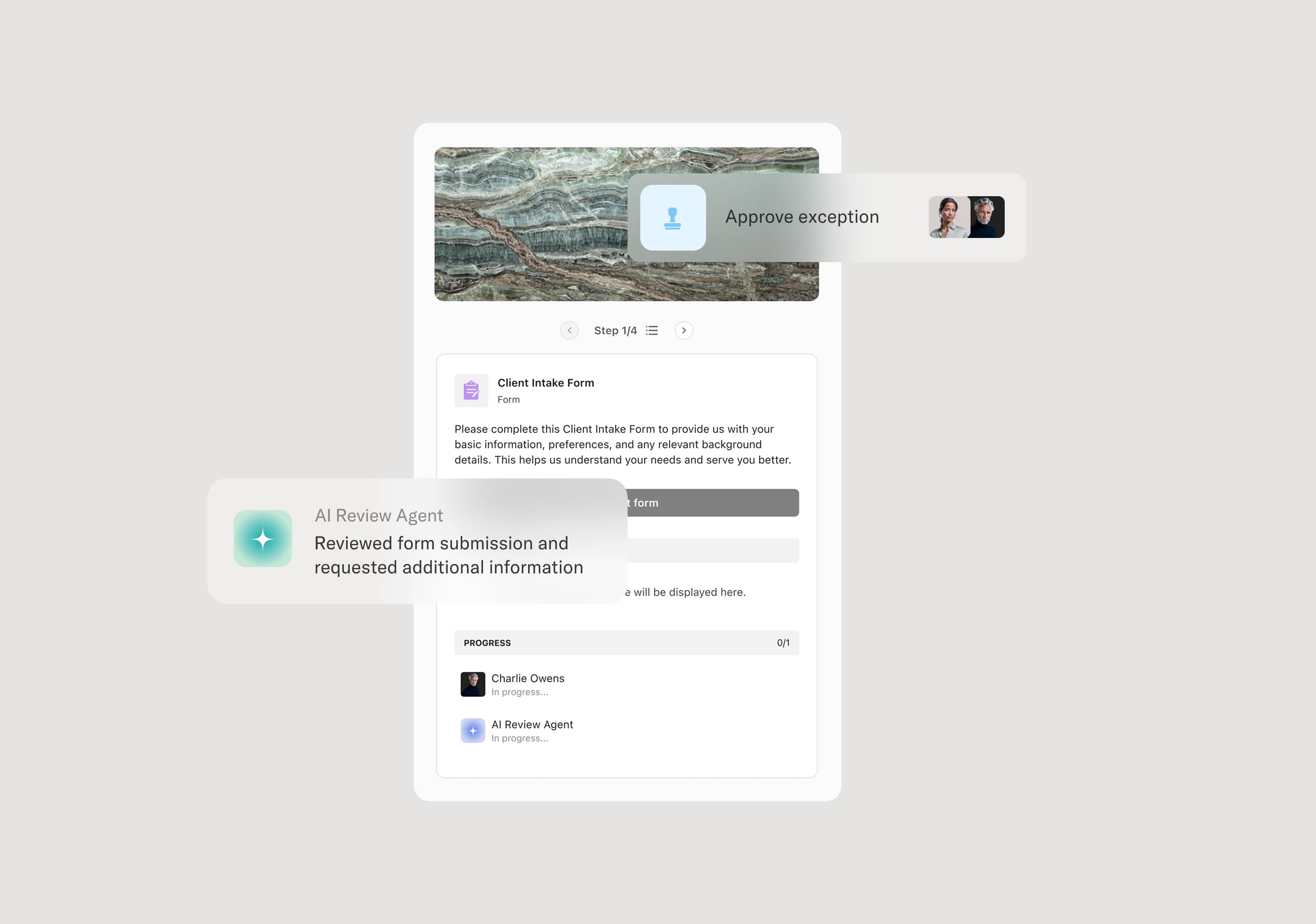
Orchestrates multi-stakeholder review across data owners, security, privacy, and legal
AI agents classify data sensitivity and identify applicable sharing policies
Tracks sharing approvals and conditions for audit and compliance
Coordinates agreement requirements when contracts must precede sharing