Release manager
DevOps lead
IT operations director
Engineering manager
Change advisory board chair
VP of engineering

When software releases are ready for production deployment. When infrastructure changes require formal approval. When regulatory environments mandate change control. When high-risk changes require management authorization. Ideal for technology organizations, regulated industries, and any enterprise with production change management requirements.
Development teams prepare releases and request deployment. QA confirms testing completion and sign-off. Operations validates deployment readiness and runbook preparation. Security reviews any security implications. Change advisory boards or management authorize significant releases.
Controlled production changes with proper authorization before deployment Reduced deployment risk through structured readiness validation Compliant change management meeting audit and regulatory requirements Clear deployment accountability with documented approval chain
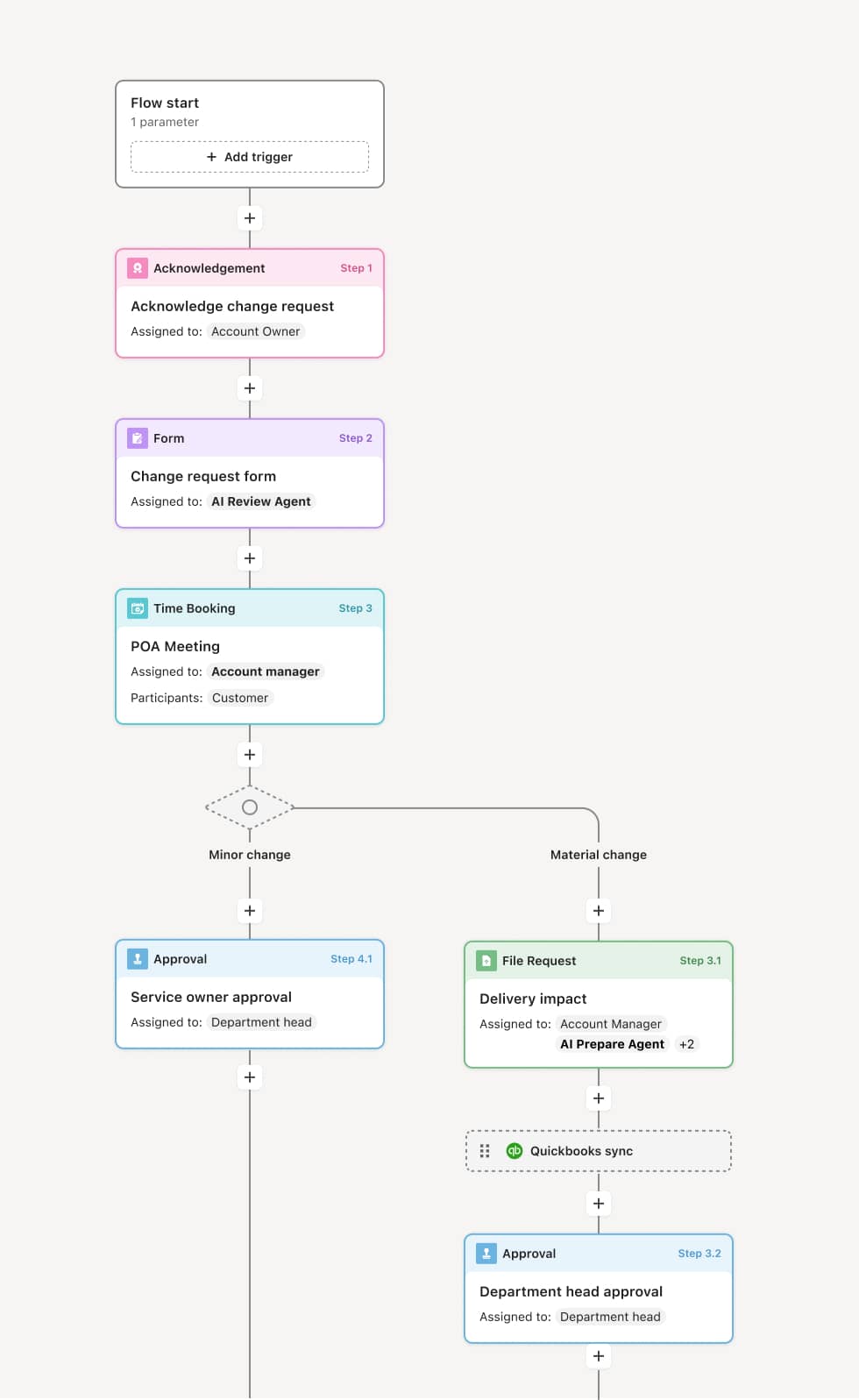
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo's flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Deployment request submission
The process begins when a deployment request is submitted including release contents, testing summary, deployment plan, and rollback procedures. AI agents may validate completeness and check for deployment window conflicts or dependency issues.
Readiness validation
Operations reviews the deployment for readiness including runbook availability, environment preparation, and monitoring setup. QA confirms all testing is complete and signed off. Any gaps must be addressed before proceeding.
Risk assessment
The deployment is assessed for risk based on scope, complexity, customer impact, and timing. High-risk deployments may require additional review or restricted deployment windows. Risk mitigation plans are documented.
Authorization decision
Based on risk level, appropriate authorization is obtained. Standard changes may follow expedited approval. Significant or high-risk changes require change advisory board or management approval. Authorization includes any conditions or restrictions.
Deployment execution authorization
Approved deployments are authorized for execution within the specified window. The deployment team confirms readiness and proceeds. Post-deployment validation confirms successful release. Any issues trigger documented incident response.
This process relies on release documentation, test results, deployment plans, and change records. Triggers include release readiness, scheduled deployment windows, or emergency change requests. Integration with CI/CD platforms like Jenkins or GitLab, ITSM tools like ServiceNow, and monitoring systems supports deployment operations.
Key decision points include determining whether readiness criteria are met, what risk level applies to the deployment, whether timing is appropriate, and whether additional authorization is required.
Deployments approved without complete testing causing production issues. Risk assessment not reflecting actual complexity. Authorization bottlenecks delaying time-sensitive releases. Rollback plans not validated before approval.
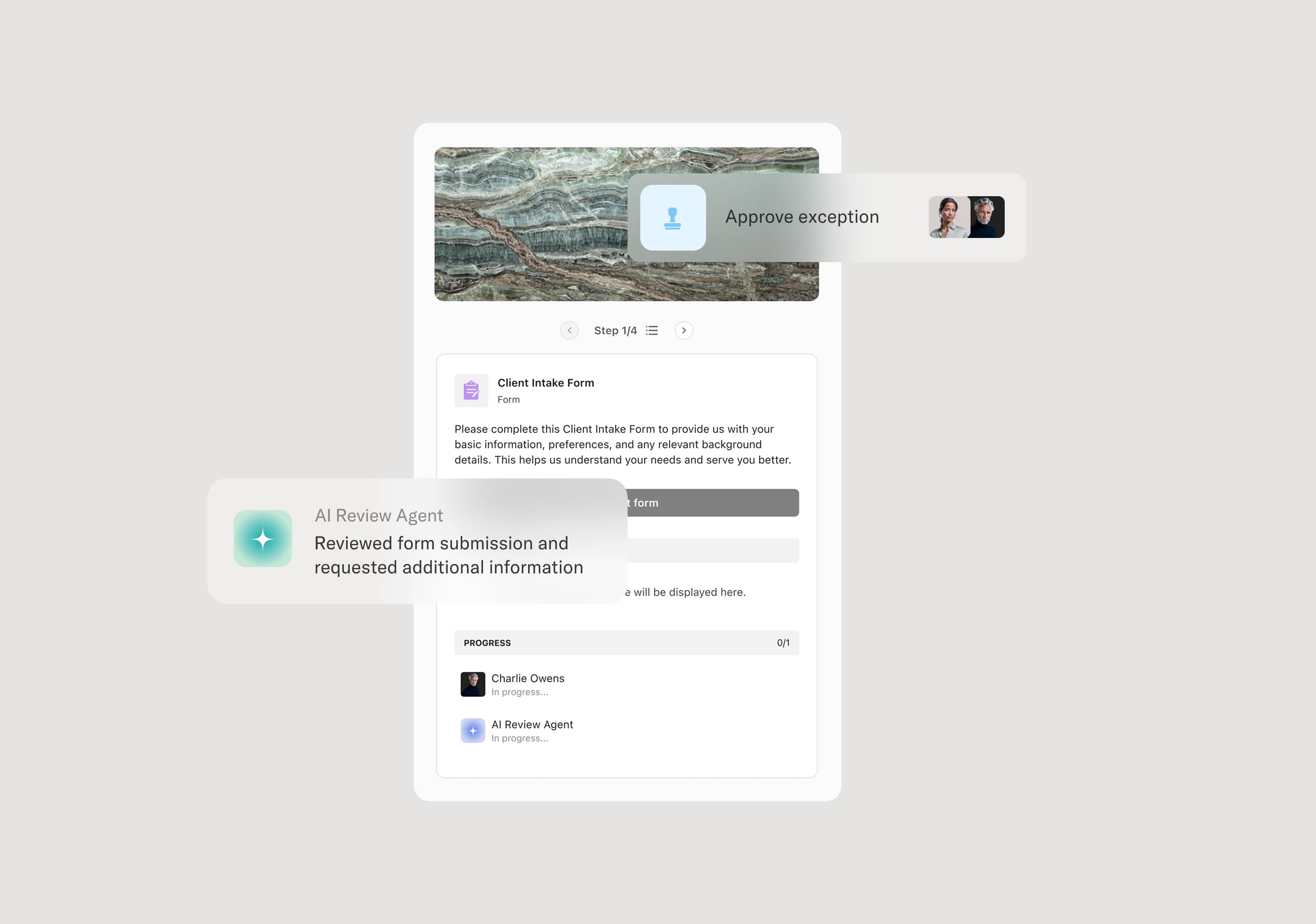
Orchestrates deployment review across development, QA, and operations with clear gates
AI agents validate deployment prerequisites and check for conflicts
Routes approvals based on risk level to appropriate authority
Maintains deployment records for audit and post-incident analysis