Fraud investigations director
Financial crimes manager
Chief risk officer
Law enforcement liaison
Fraud analytics lead
Compliance director

This process is used when suspected external fraud activity — identified through transaction monitoring, customer reports, or business unit referrals — is escalated beyond routine case handling because it involves complex schemes, multiple accounts, organized fraud activity, or material financial exposure. It applies when the investigation must examine fraud methodology, identify all affected accounts, quantify losses, preserve evidence for potential prosecution, and produce findings that inform prevention improvements. Ideal for banks, insurers, payment networks, e-commerce companies, and any organization managing significant external fraud exposure.
The fraud investigation process typically involves senior fraud investigators who lead the analysis, fraud analytics teams who support pattern identification and data analysis, legal counsel who advises on evidence preservation and law enforcement coordination, law enforcement liaisons who manage referrals and cooperation, and business unit leaders who implement remediation and control improvements based on findings.
Comprehensive understanding of the fraud scheme including methodology, scope, affected accounts, and responsible parties. Quantified financial exposure with documented losses for recovery, insurance claims, and financial reporting. Preserved evidence that supports law enforcement prosecution and civil recovery efforts. Actionable fraud prevention intelligence that informs control improvements, detection model tuning, and policy updates. Coordinated law enforcement engagement through professional referrals with well-documented case packages.
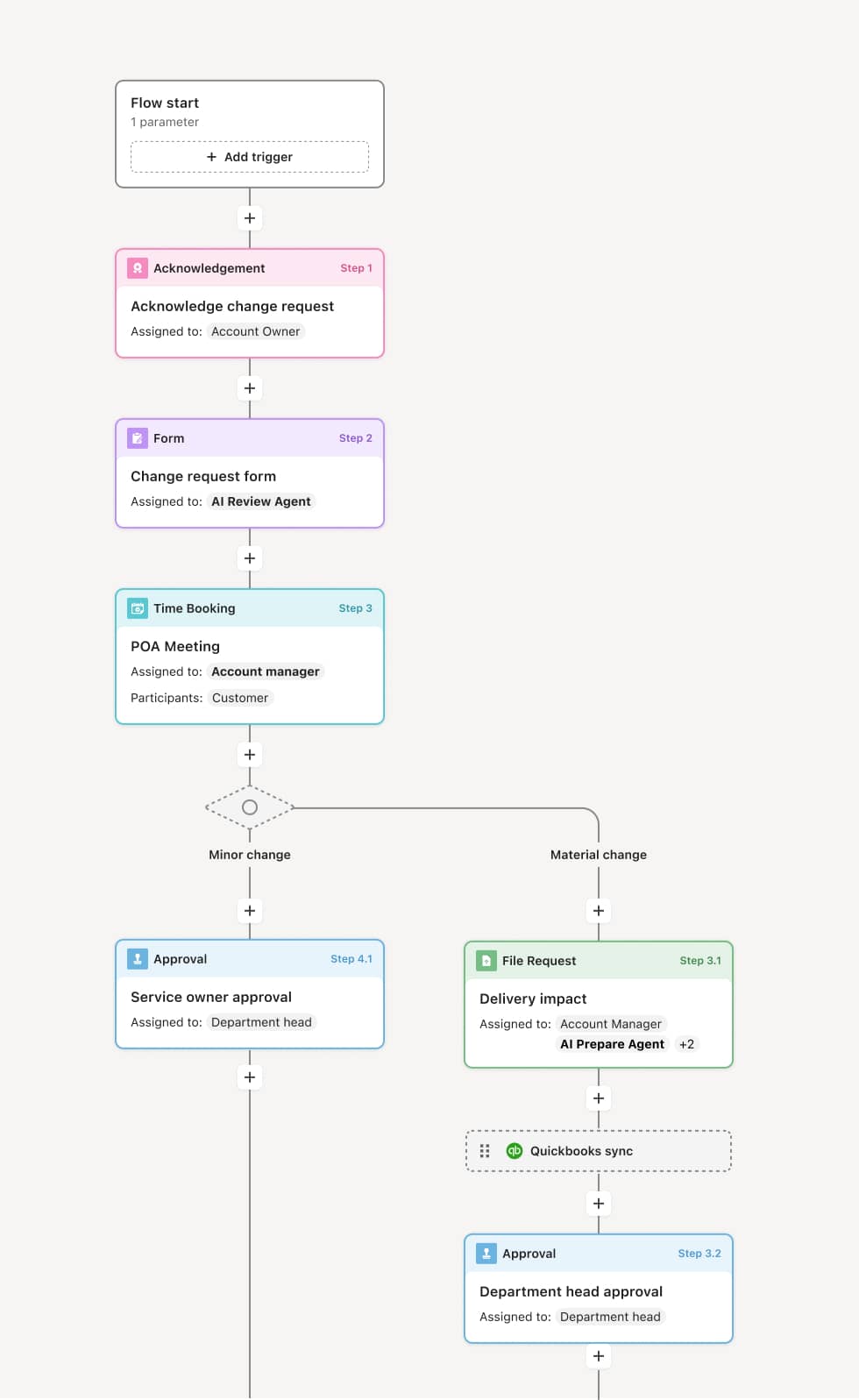
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo’s flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Case escalation and investigation scoping
The process begins when a suspected fraud case is escalated for formal investigation due to complexity, dollar exposure, or organized activity indicators. The lead investigator reviews the referral data and defines the investigation scope, including the accounts, transactions, time period, and fraud typology. An AI Agent can assist by compiling the referral data, related alerts, and linked accounts into an initial investigation package.
Data analysis and pattern identification
The investigation team conducts deep data analysis, examining transaction flows, account opening patterns, device fingerprints, geographic indicators, and timing anomalies. Fraud analytics tools are used to identify linked accounts, common identities, and network connections that indicate organized activity. An AI Agent may surface account clusters and transaction patterns consistent with known fraud typologies.
Evidence collection and documentation
The team collects and preserves evidence including transaction records, account applications, identity documents, communications, device data, and surveillance material. Evidence is documented with chain-of-custody records and organized for potential law enforcement use.
Loss quantification and impact assessment
The investigator quantifies the financial impact of the fraud, including direct losses, recovery potential, and exposure across all identified accounts. The impact assessment includes both realized and potential losses, and identifies accounts that require immediate protective action.
Findings and recommendations
The lead investigator prepares a comprehensive findings report documenting the fraud scheme, methodology, affected accounts, financial impact, and responsible parties. The report includes recommendations for control improvements, detection model updates, and prevention measures to address the vulnerability exploited by the scheme.
Law enforcement referral and recovery
If the investigation supports prosecution, the law enforcement liaison prepares a case referral package and coordinates with the appropriate agency. Civil recovery actions — such as asset recovery, insurance claims, or litigation — are initiated based on legal counsel’s advice. The case is closed with a complete record preserved.
This process commonly relies on inputs such as escalated case data, transaction records, account applications, identity verification records, device and authentication data, and fraud analytics outputs. It may be triggered by escalation from fraud case management, detection system alerts, or law enforcement inquiries. Connected systems often include fraud analytics platforms, case management systems, core banking systems, identity verification tools, and law enforcement referral portals.
Key decision points include whether the escalated case warrants a formal investigation based on complexity, exposure, or organized activity indicators, how broadly the investigation scope should extend based on linked accounts and network analysis, whether the evidence supports law enforcement referral and prosecution, and what control improvements are needed to prevent recurrence of the identified fraud methodology.
Investigation scope defined too narrowly, missing linked accounts and the full extent of the fraud ring. Data analysis limited to the initially reported accounts without exploring network connections and common patterns. Evidence not preserved to a standard that supports law enforcement use, reducing prosecution potential. Findings report focused only on the specific case without translating findings into actionable prevention recommendations. Law enforcement referral delayed or not made because the case package was not prepared to agency standards.
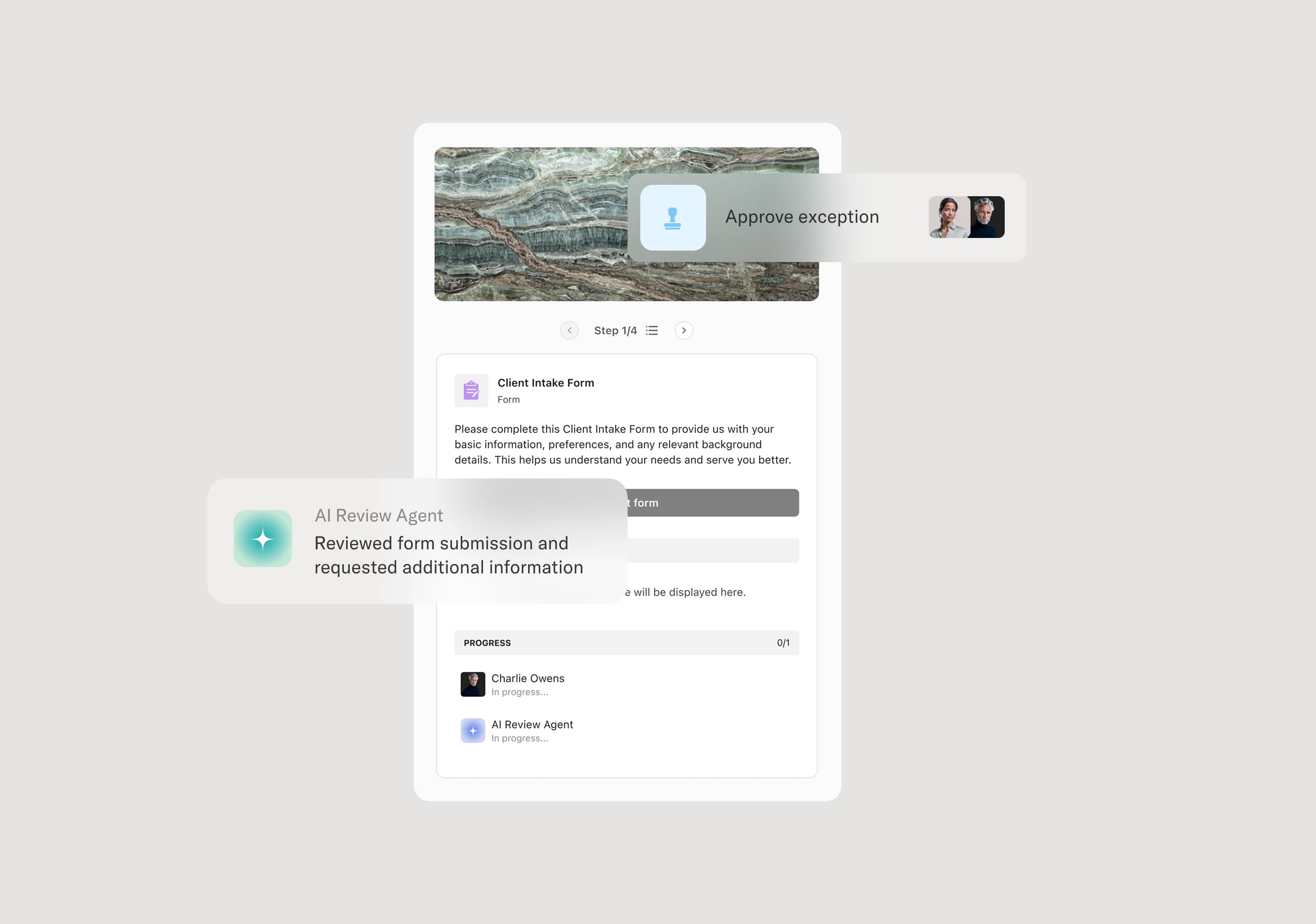
Orchestrates external fraud investigation from escalation through law enforcement referral across investigators, analytics, legal, and business units in a single coordinated flow.
AI Agents compile investigation packages at case opening and surface linked accounts, transaction patterns, and network connections during analysis.
Manages evidence collection and preservation within the workflow with chain-of-custody documentation and organized case files.
Coordinates law enforcement referrals within the workflow, assembling case packages and tracking agency engagement.
Connects to fraud analytics, core banking, and case management platforms so investigation data, account records, and referral documentation are managed in context.
Preserves the complete investigation record including analysis, evidence, findings, loss quantification, recommendations, and law enforcement coordination for legal, regulatory, and organizational reference.