HIPAA privacy officer
IT security incident lead
Compliance director
Legal counsel
Chief information security officer
Risk management officer

This process is used when the organization detects or is alerted to a security incident that may involve unauthorized access, use, disclosure, or loss of protected health information. It applies when the incident must be contained, investigated to determine scope and impact, assessed under HIPAA’s breach definition and risk assessment framework, and — if a breach is confirmed — reported to affected individuals, HHS OCR, and potentially the media within required timelines. It is common when IT security, privacy, compliance, legal, and operational leaders must coordinate under regulatory time pressure. Ideal for healthcare providers, health plans, clearinghouses, and business associates managing PHI security incidents.
The incident response process typically involves IT security staff who detect and contain the incident, the privacy officer who leads the breach determination and notification process, compliance coordinators who document the investigation and reporting, legal counsel who advises on breach determination and liability, and operational leaders who implement corrective actions in affected areas.
Rapid incident containment that limits the scope and impact of unauthorized PHI access or disclosure. Accurate breach determination through the required four-factor risk assessment that evaluates whether notification is required. Timely regulatory notification to affected individuals, HHS OCR, and media when applicable, within HIPAA’s 60-day timeline. Thorough root cause analysis that identifies how the incident occurred and what systemic factors contributed. Documented corrective actions that address the root cause and reduce the risk of recurrence.
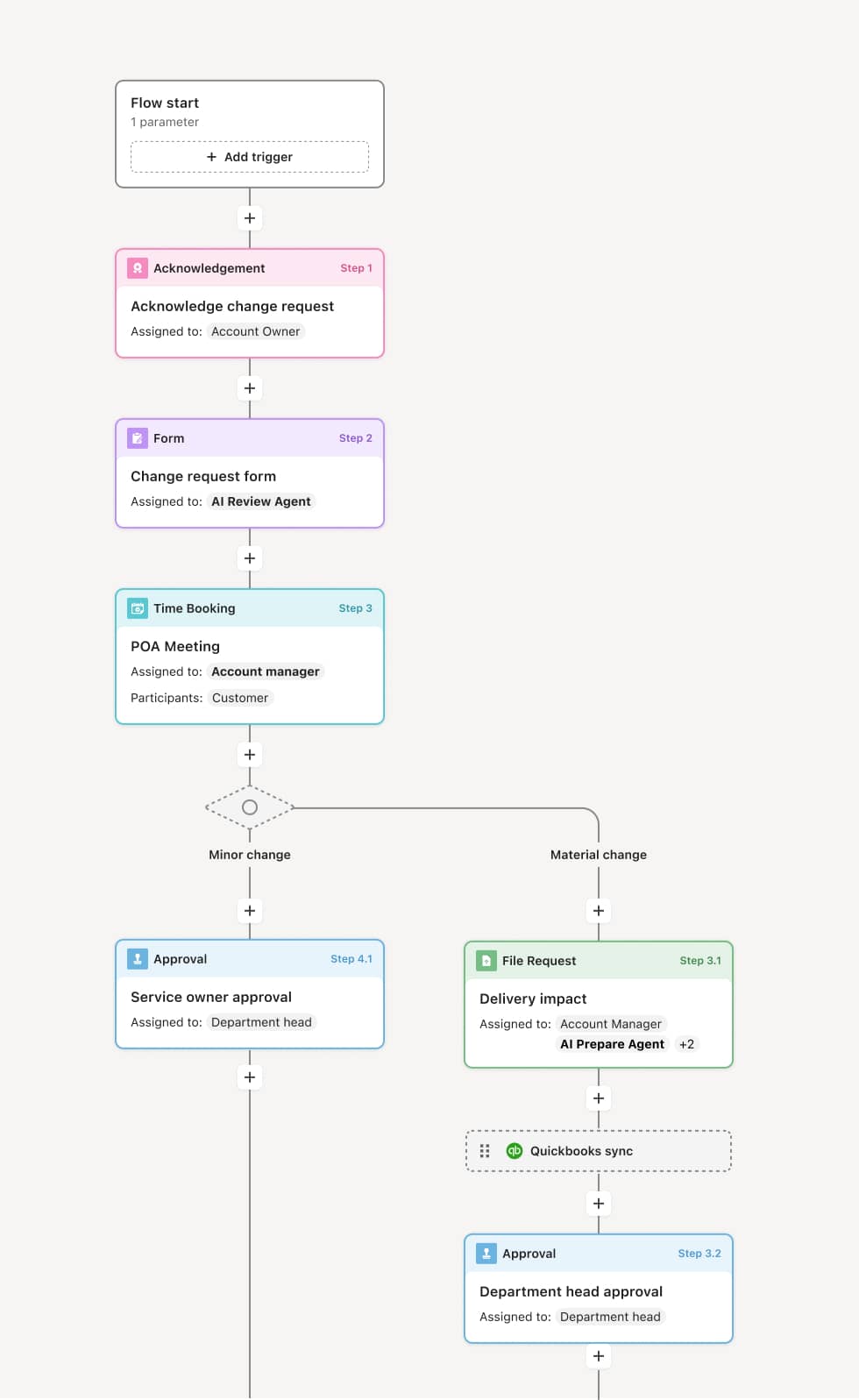
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo’s flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Incident detection and initial containment
The process begins when a security incident involving PHI is detected — through system alerts, workforce reporting, audit log review, or external notification. IT security takes immediate containment actions to stop the unauthorized access or disclosure and preserve evidence. The incident is logged with the date, time, nature, and initial scope. An AI Agent can assist by compiling system access logs, affected records, and the user activity timeline for the investigation team.
Investigation and scope determination
The privacy officer and IT security team investigate the incident to determine what PHI was involved, who accessed it, how the access occurred, and whether the information was actually viewed or acquired. The investigation includes reviewing access logs, interviewing involved parties, and assessing the technical and physical circumstances.
Breach risk assessment
The privacy officer conducts the HIPAA four-factor risk assessment to determine whether the incident constitutes a reportable breach: evaluating the nature and extent of PHI involved, the unauthorized person who accessed it, whether PHI was actually acquired or viewed, and the extent to which risk has been mitigated. If the assessment determines that there is a low probability that the PHI was compromised, no notification is required. If a breach is confirmed, notification obligations are triggered.
Notification preparation and execution
If a breach is confirmed, the organization prepares and sends notification to affected individuals within 60 days of discovery. For breaches affecting 500 or more individuals, HHS OCR and prominent media outlets must also be notified. Notification letters include the description of the breach, types of PHI involved, steps individuals should take, and the organization’s response.
Corrective action and remediation
Based on the root cause analysis, the organization implements corrective actions to address the vulnerability or process failure that led to the incident. Corrective actions may include system patches, access control changes, workforce retraining, or policy updates. An AI Agent may track remediation tasks to completion and verify implementation.
Documentation and regulatory reporting
The complete incident record — including detection, investigation, risk assessment, breach determination, notification, and corrective actions — is preserved. For breaches affecting fewer than 500 individuals, the annual breach log is submitted to HHS OCR.
This process commonly relies on inputs such as system access logs, incident reports, PHI inventory data, workforce interviews, and the four-factor risk assessment. It may be triggered by a system alert, a workforce report, an audit finding, or an external notification. Connected systems often include SIEM (security information and event management) tools, compliance management platforms, incident tracking systems, and notification management tools.
Key decision points include whether the incident involves PHI and warrants a formal investigation, what the scope of PHI involved in the incident is, whether the four-factor risk assessment determines that a reportable breach has occurred, and what corrective actions are necessary to address the root cause and reduce recurrence risk.
Incidents not reported promptly by the workforce, delaying containment and compressing the investigation timeline. Investigation scope underestimated, leading to an incomplete understanding of the PHI involved. Four-factor risk assessment not documented thoroughly, weakening the organization’s position if the determination is challenged. Notification deadlines missed because the investigation took too long or the notification process was not initiated promptly. Corrective actions not implemented or verified, leaving the root cause vulnerability in place.
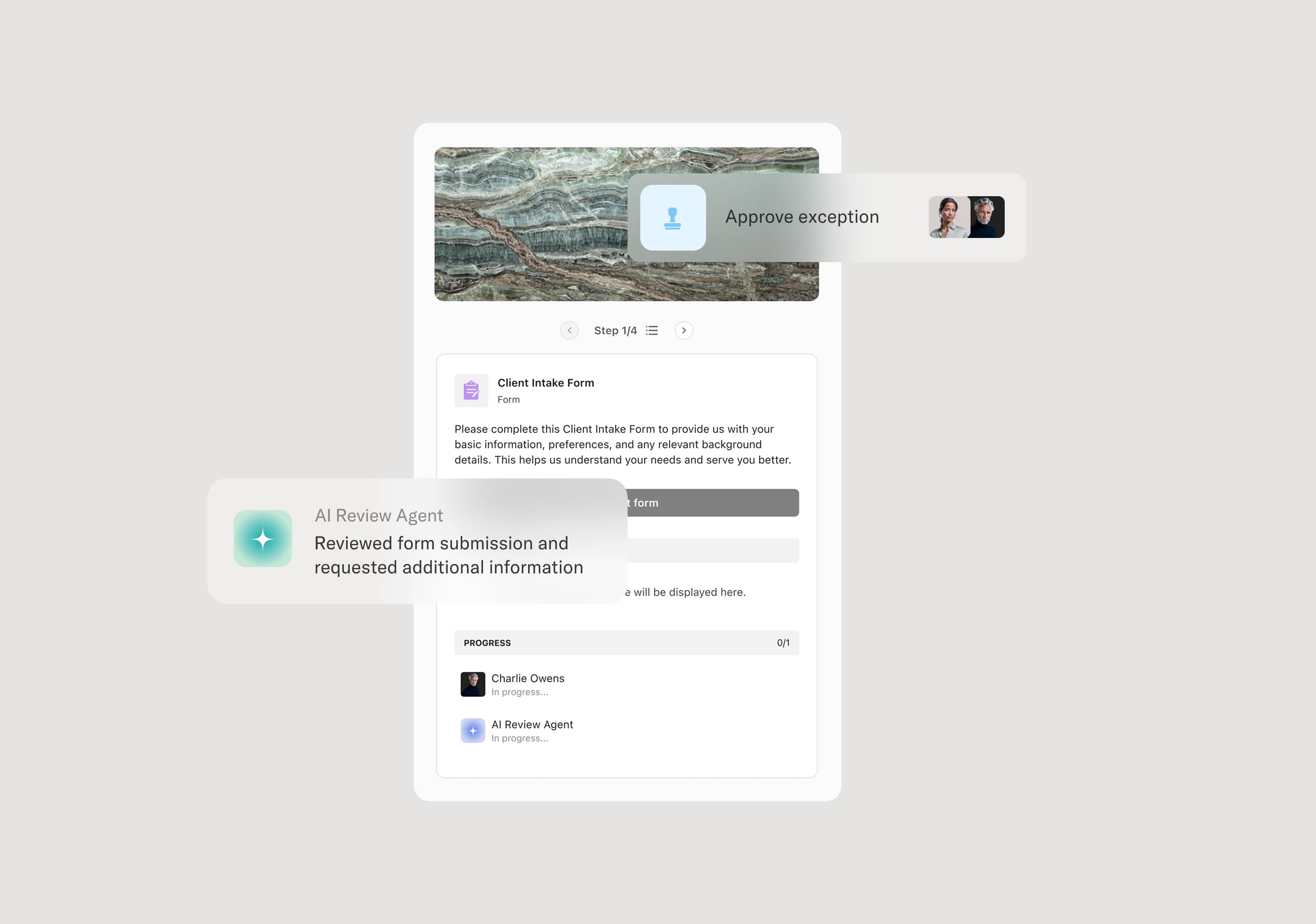
Orchestrates incident response from detection through corrective action across IT security, privacy, compliance, legal, and operational teams in a single coordinated flow.
Triggers the investigation workflow immediately upon incident identification, ensuring containment actions and evidence preservation begin without delay.
AI Agents compile access logs, affected records, and user activity timelines for the investigation team, accelerating the scope determination.
Tracks the 60-day notification timeline from the date of breach discovery, ensuring notification preparation and execution are completed on schedule.
Manages corrective action implementation within the workflow, tracking each remediation task to completion and verification.
Preserves the complete incident record including detection, investigation, risk assessment, breach determination, notifications, and corrective actions for OCR reporting and audit readiness.