Compliance officer
Risk manager
Operations director
General counsel
Department head
Chief operating officer

This process is used when a team or individual needs to deviate from an established policy to address a specific business situation that the policy does not adequately accommodate. It is triggered when a standard process cannot proceed under existing rules, when a client or partner requirement conflicts with internal policy, or when operational circumstances create a legitimate need for a one-time or time-limited deviation. Policy exception approval is especially important in regulated industries, when exceptions carry financial or legal risk, or when the deviation could set a precedent. It is relevant across financial services, healthcare, insurance, government, professional services, and any organization with formal policy governance.
Policy exception approval typically involves the requestor who identifies the need and provides business justification, the policy owner who evaluates the request against the intent and scope of the original policy, a risk or compliance reviewer who assesses potential exposure, and a senior leader or governance committee that provides final authorization. Legal counsel may also be involved when the exception involves regulatory obligations or contractual commitments.
Controlled deviation without policy erosion by ensuring every exception is individually assessed and authorized rather than informally bypassed. Documented risk acceptance with the business justification, risk assessment, and approval decision captured as a formal governance record. Faster exception resolution by routing requests directly to the appropriate authority rather than relying on ad hoc email chains or meetings. Visibility into exception patterns so governance teams can identify recurring exceptions that may indicate a need to update the underlying policy.
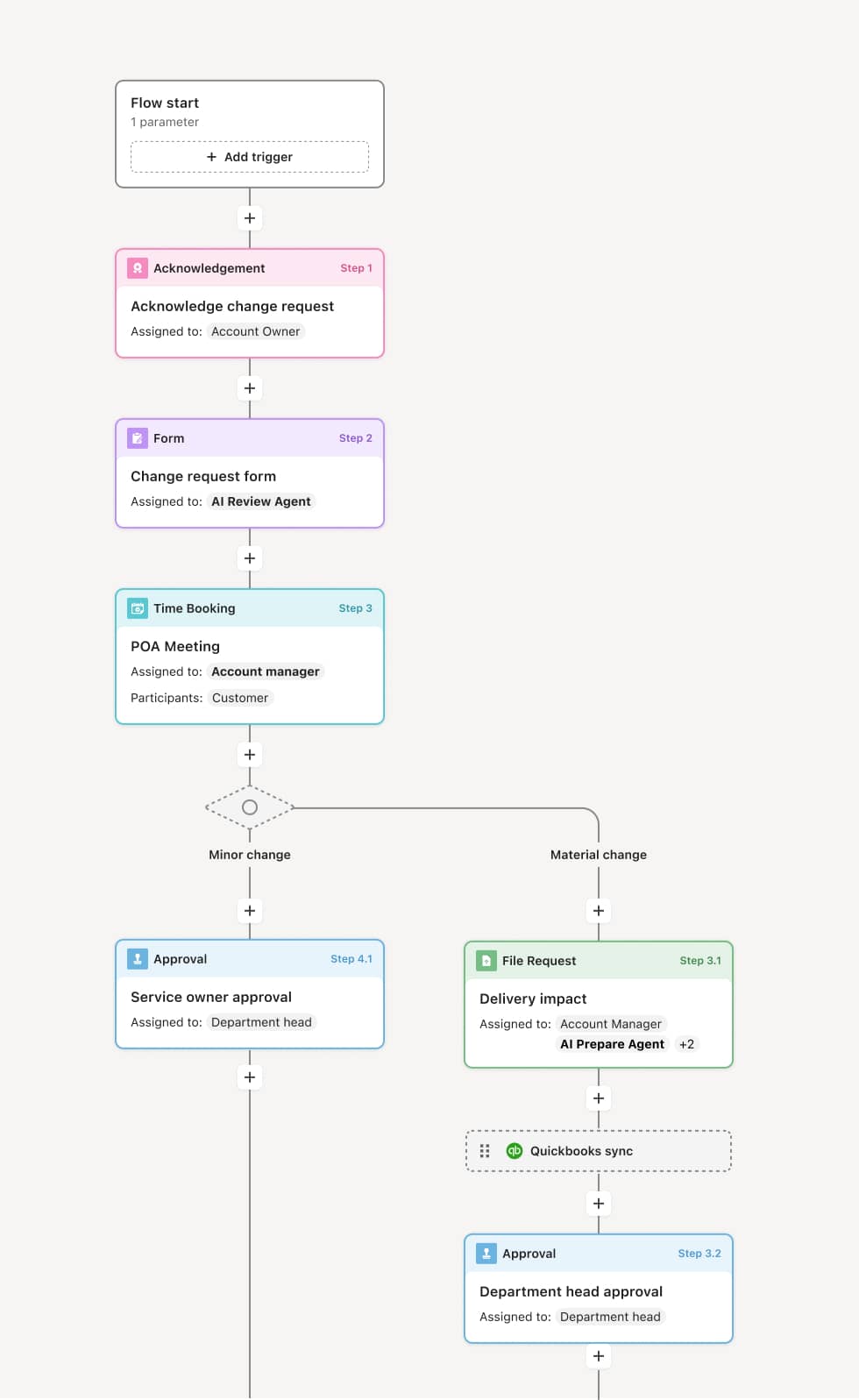
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo’s flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Exception request and justification
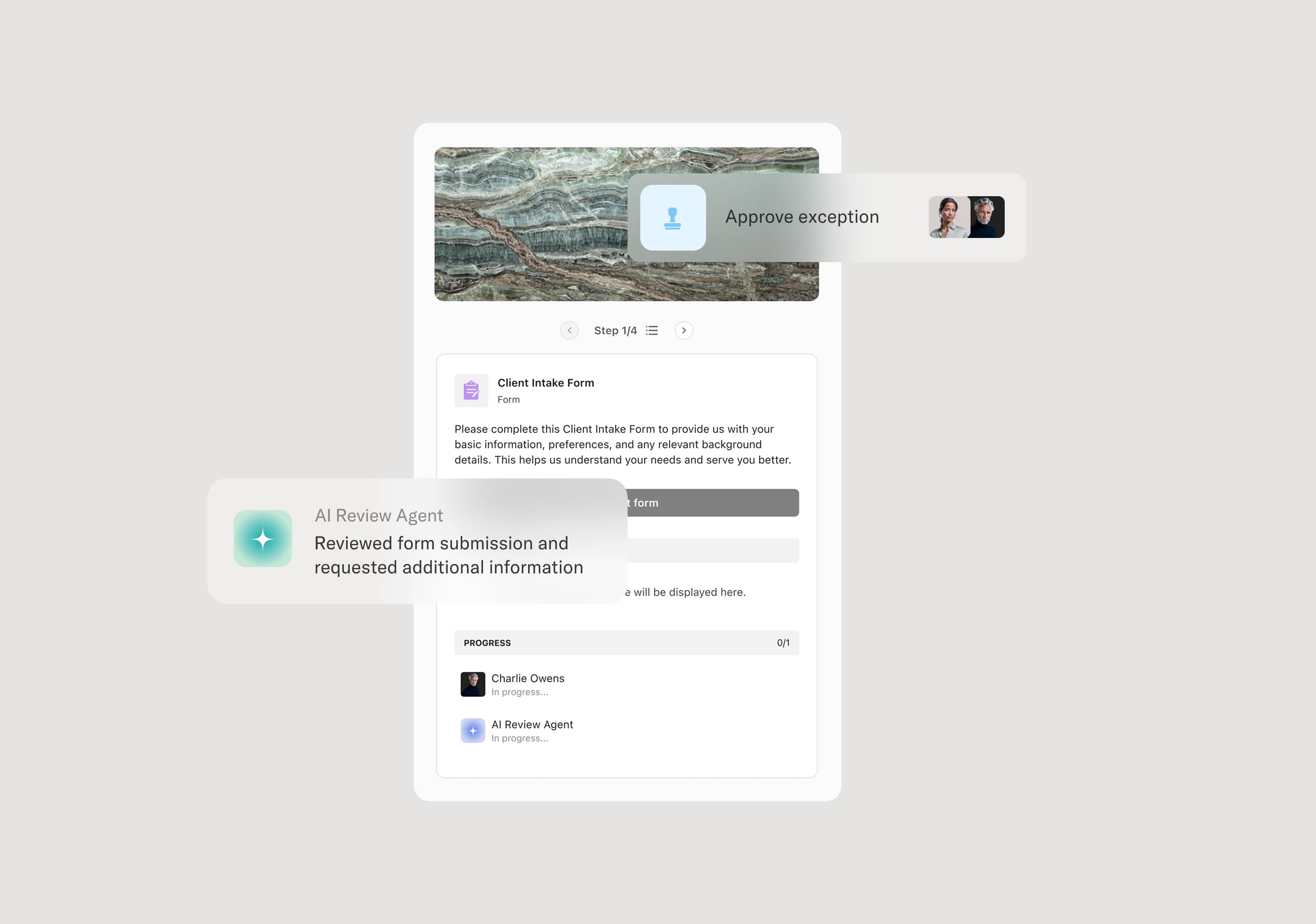
The process begins when a requestor identifies a situation that requires deviation from an existing policy. The request includes the specific policy in question, the nature of the deviation, the business justification, the proposed duration or scope of the exception, and any compensating controls or mitigations the requestor proposes. An AI Agent may assist by validating that the request is complete, identifying the relevant policy, and flagging whether similar exceptions have been requested or granted previously.
Policy owner review
The exception request is routed to the owner of the affected policy, who evaluates whether the requested deviation is consistent with the policy’s underlying intent. The policy owner considers whether the exception is narrow and time-limited, whether it creates risk for other processes or stakeholders, and whether the proposed compensating controls are adequate. If the request is incomplete or the justification insufficient, it is returned to the requestor with specific feedback. If the policy owner determines the exception is within their authority, they may approve it directly. Otherwise, the request moves forward for additional review.
Risk and compliance assessment
For exceptions that carry financial, legal, or regulatory risk, the request is routed to a risk or compliance reviewer. This reviewer evaluates the potential exposure, considers whether the exception could trigger audit findings or regulatory scrutiny, and assesses whether the compensating controls are sufficient. An AI Agent may prepare a risk context summary, including the policy’s history of prior exceptions and any related incidents, to support the reviewer’s assessment. If the risk is deemed unacceptable, the reviewer may recommend denial or require additional mitigations before the request can proceed.
Authorization
With the policy owner and risk assessment complete, the exception request is routed to the appropriate authority for final authorization. This may be a senior leader, a governance committee, or an executive sponsor, depending on the severity and scope of the exception. The approver reviews the complete package, including the request, business justification, policy owner assessment, and risk review, before granting or denying the exception. If approved, the authorization specifies the scope, duration, and any conditions attached to the exception.
Documentation and monitoring
Once authorized, the exception is formally documented, including the approved scope, duration, conditions, and the identity of the authorizing party. The requestor and relevant stakeholders are notified, and the exception is tracked through its effective period. If the exception is time-limited, the process includes a scheduled review or expiration trigger. All request details, assessments, and authorization records are retained as a structured governance record.
This process commonly relies on inputs such as the exception request form, the relevant policy document, business justification materials, risk assessment data, and records of prior exceptions. It may be triggered by an operational need, a client request, or an audit finding. Systems such as a GRC platform like ServiceNow or Archer, a policy management tool, or SharePoint may provide policy documents, risk data, and exception tracking history.
Key decision points include whether the business justification is sufficient to warrant a deviation, whether the policy owner can authorize the exception within their scope or whether escalation is required, whether the risk and compliance assessment identifies unacceptable exposure, and whether the exception should be time-limited or subject to specific conditions.
Vague business justification, when the requestor does not articulate why the exception is necessary, making it difficult for reviewers to assess the request. Informal bypasses, when teams circumvent the exception process entirely because the formal path is perceived as too slow or burdensome. Missing risk assessment, when exceptions are approved without a structured evaluation of potential exposure, leaving the organization unaware of accumulated risk. Expired exceptions without review, when time-limited exceptions are not revisited at expiration, allowing deviations to persist indefinitely.
Orchestrates the full exception lifecycle from request submission through policy owner review, risk assessment, authorization, and monitoring in a single coordinated process.
AI Agents validate request completeness and surface prior exception history so reviewers enter each assessment with full context rather than starting from scratch.
Routes exceptions to the appropriate authority based on risk level and policy scope ensuring low-risk exceptions move quickly while high-risk cases receive the required level of scrutiny.
Extends existing GRC and policy management systems such as ServiceNow, Archer, or SharePoint by connecting policy documents and exception records directly into the approval workflow.
Captures a complete record of every request, assessment, authorization, and condition so governance teams can trace any active exception back to its documented basis and approval chain.