IT security manager
Identity and access management lead
System administrator
Chief information security officer
Compliance officer
IT operations director

This process is used when an individual requires elevated access to systems, databases, infrastructure, or applications beyond what their standard role provides. It is triggered when a developer needs production database access for incident resolution, when an administrator requires root or domain-level permissions for maintenance, when a consultant needs temporary access to client systems, or when an audit identifies that access reviews require formal approval workflows. Privileged access approval is especially critical in environments subject to SOC 2, ISO 27001, HIPAA, PCI-DSS, or other security frameworks. It is relevant across all industries where sensitive systems, data, or infrastructure must be protected from unauthorized access.
Privileged access approval typically involves the requestor who provides business justification, the requestor’s manager who confirms the business need, an IT security or IAM team that evaluates the request against security policy, the system owner who authorizes access to their specific system, and a compliance or audit team that may review high-risk grants. For emergency or break-glass access, a designated on-call approver may be involved.
Controlled elevation of privileges by requiring explicit justification and multi-party authorization before any elevated access is granted. Reduced attack surface through time-bounded access grants and automatic expiration that prevent standing privileged access from accumulating. Regulatory compliance with a documented approval trail that satisfies auditor requirements for privileged access management under SOC 2, ISO 27001, and similar frameworks. Faster incident response by providing a structured emergency access path that grants privileges quickly while maintaining accountability and post-incident review.
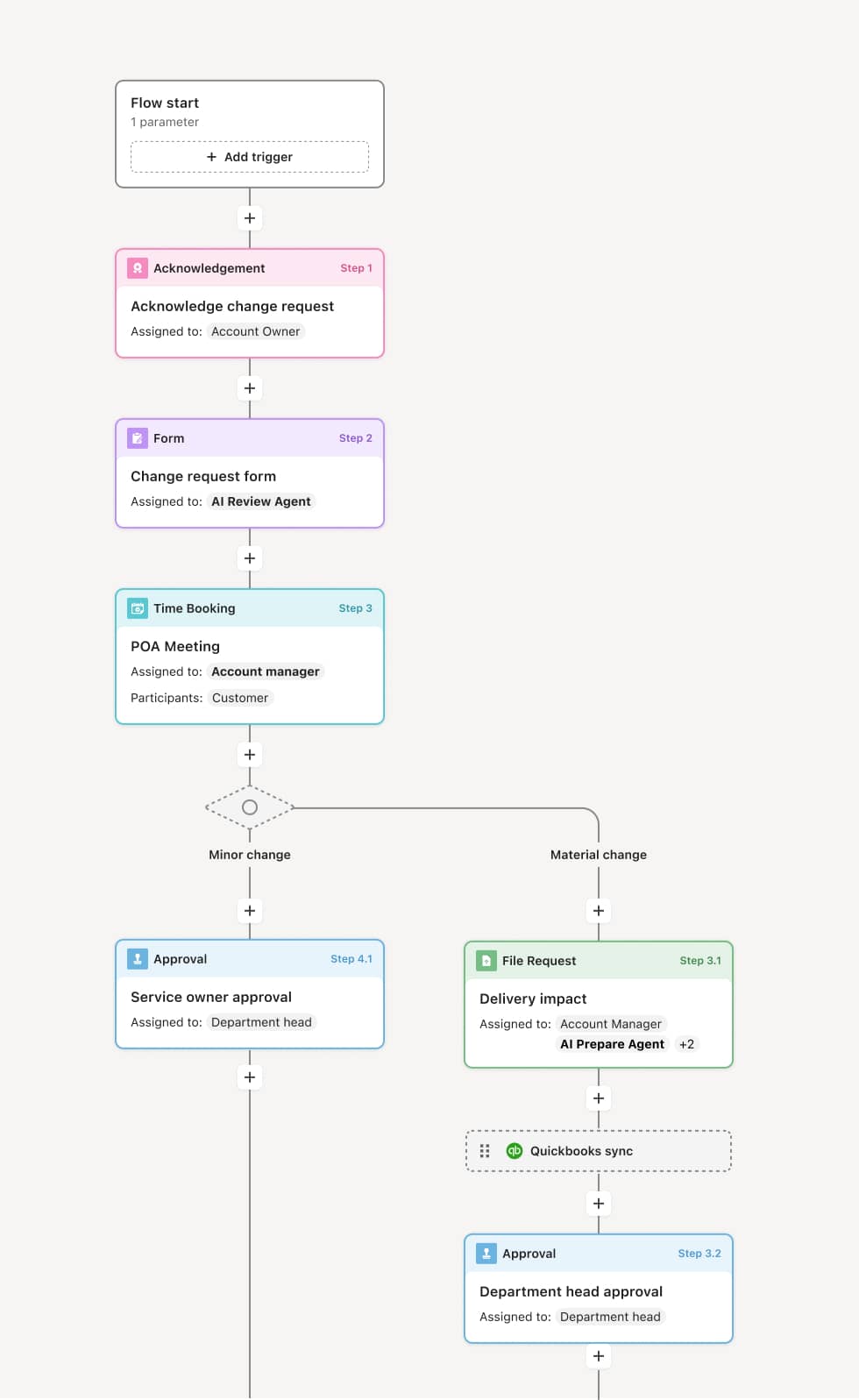
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo’s flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
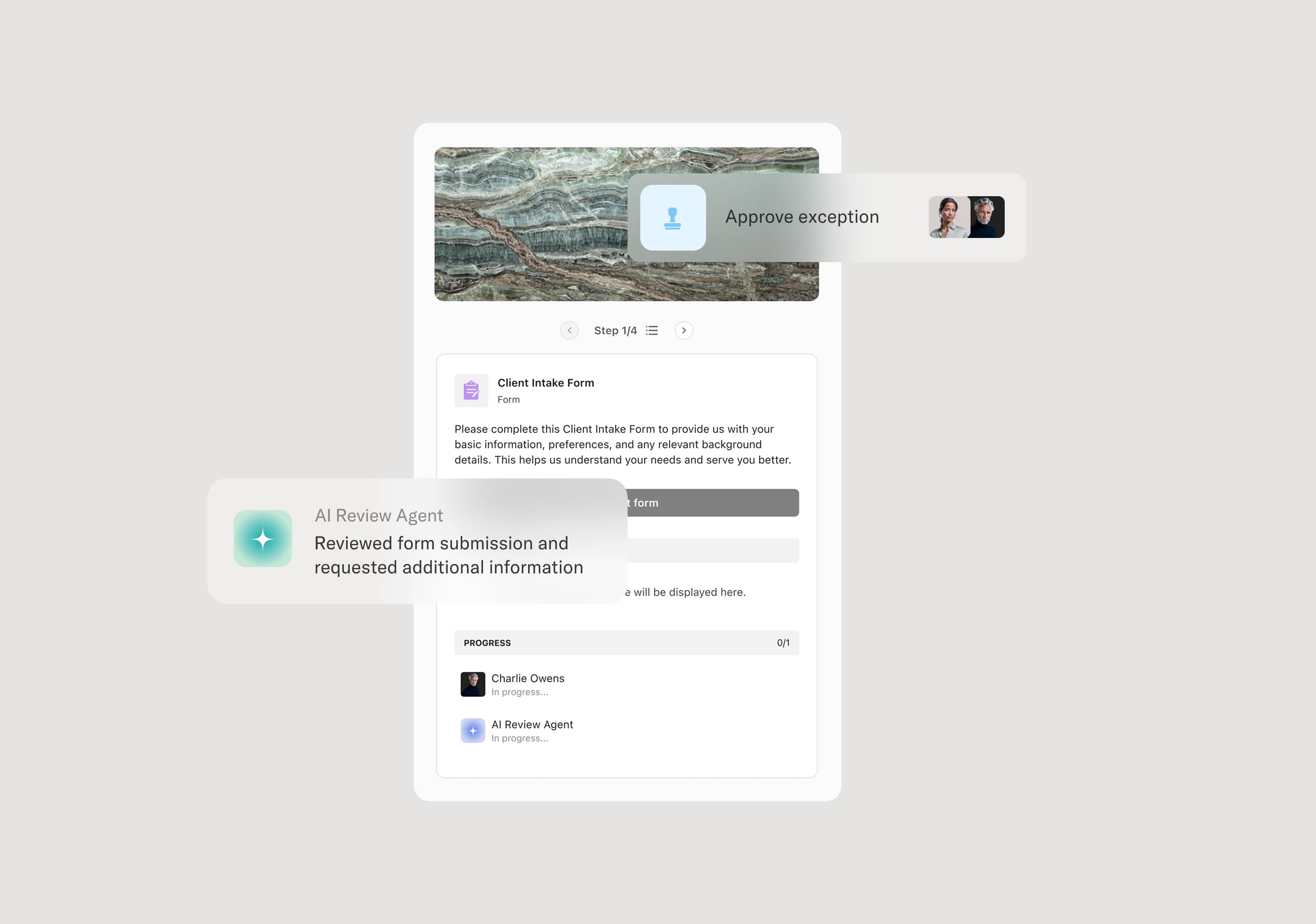
Access request and justification
The process begins when an individual submits a request for privileged access, specifying the system or resource, the level of access required, the business justification, and the requested duration. An AI Agent may assist by pre-populating system details based on the request, checking whether the requestor already holds conflicting access, and flagging if the requested access level exceeds what is typically granted for the stated purpose.
Manager confirmation
The request is routed to the requestor’s manager, who confirms that the business need is legitimate and that the access request is consistent with the individual’s current responsibilities. If the manager does not confirm, the request is returned to the requestor. For emergency or break-glass scenarios, this step may be expedited or deferred to a post-access review.
Security and policy evaluation
The IT security or IAM team evaluates the request against the organization’s access control policy, the principle of least privilege, and any applicable regulatory requirements. This includes assessing whether the requested access level is appropriate for the stated task, whether compensating controls such as session monitoring are required, and whether the request conflicts with separation-of-duties rules. If the request requires adjustment, the security team returns it with a recommended scope reduction.
System owner authorization
The system owner for the targeted resource reviews and authorizes the access grant. The system owner is the individual or team accountable for the data, application, or infrastructure being accessed and is responsible for confirming that the access is appropriate for their system. If the system owner identifies concerns, the request may be modified or denied.
Access provisioning, monitoring, and revocation
Once all approvals are in place, access is provisioned with the specified scope, conditions, and time limit. The provisioning event is logged, and any required compensating controls such as session recording or activity alerts are activated. When the access period expires or the task is completed, access is automatically revoked. A post-access review may be triggered for high-risk grants to confirm that the access was used appropriately and that no security events occurred during the access period.
This process commonly relies on inputs such as the access request form, user identity and role data, system and resource inventories, access control policies, and audit or compliance requirements. It may be triggered by an incident, a project requirement, a maintenance window, or a periodic access recertification. Systems such as Okta, CyberArk, SailPoint, or Azure Active Directory may provide identity data, entitlement records, and provisioning capabilities.
Key decision points include whether the business justification supports the requested access level, whether the requested permissions comply with least-privilege and separation-of-duties policies, whether the access should be time-bounded or permanent, whether compensating controls are required, and whether the request warrants post-access review.
Standing privileged access, when time-limited grants are not revoked at expiration, allowing elevated permissions to persist indefinitely. Overly broad access grants, when the approved scope exceeds what is necessary for the stated task because the review did not enforce least-privilege principles. Emergency access without post-review, when break-glass access is granted during an incident but no post-incident review confirms the access was used appropriately. Incomplete audit trails, when access grants are provisioned outside the formal process, leaving gaps in the compliance record.
Orchestrates the full privileged access lifecycle from request submission through manager confirmation, security evaluation, system owner authorization, provisioning, and revocation in a single coordinated process.
AI Agents check requests against policy and flag conflicts such as separation-of-duties violations or access levels that exceed what is typical for the stated justification.
Supports time-bounded access with automatic expiration triggers so elevated privileges do not persist beyond their approved window.
Extends existing IAM and security platforms such as Okta, CyberArk, or SailPoint by connecting identity data and provisioning actions directly into the approval workflow.
Captures a complete record of every request, evaluation, authorization, and revocation event providing a continuous audit trail that satisfies compliance frameworks including SOC 2, ISO 27001, and PCI-DSS.