Information security manager
IT operations lead
Chief information security officer
Compliance officer
Project manager
Systems administrator

This process is used when a proposed action — such as a new tool deployment, a system configuration change, a vendor integration, or a data handling modification — requires security review before implementation. It applies when the change may affect data confidentiality, integrity, or availability, or when organizational policy mandates security sign-off for certain categories of change. It is common when security, IT, and compliance teams must coordinate their assessments within defined SLAs. Ideal for technology, financial services, healthcare, government, and any organization with formal information security governance.
The security approval process typically involves the requester who submits the change or request, security analysts or engineers who conduct the technical risk assessment, IT operations staff who evaluate implementation impact, compliance officers who assess regulatory alignment, and the CISO or security leadership who authorize high-risk or policy-exception changes.
Faster security disposition by routing requests to the right review team based on risk category and change type, avoiding blanket escalation. Documented security decisions so every approved change has a recorded risk assessment, conditions, and accountable approver. Consistent policy enforcement across all change types, reducing the risk of shadow IT or unapproved tool adoption. Reduced implementation delays by providing clear requirements and structured review paths rather than ad-hoc security consultations. Stronger compliance posture because security approvals are traceable, auditable, and aligned with regulatory frameworks.
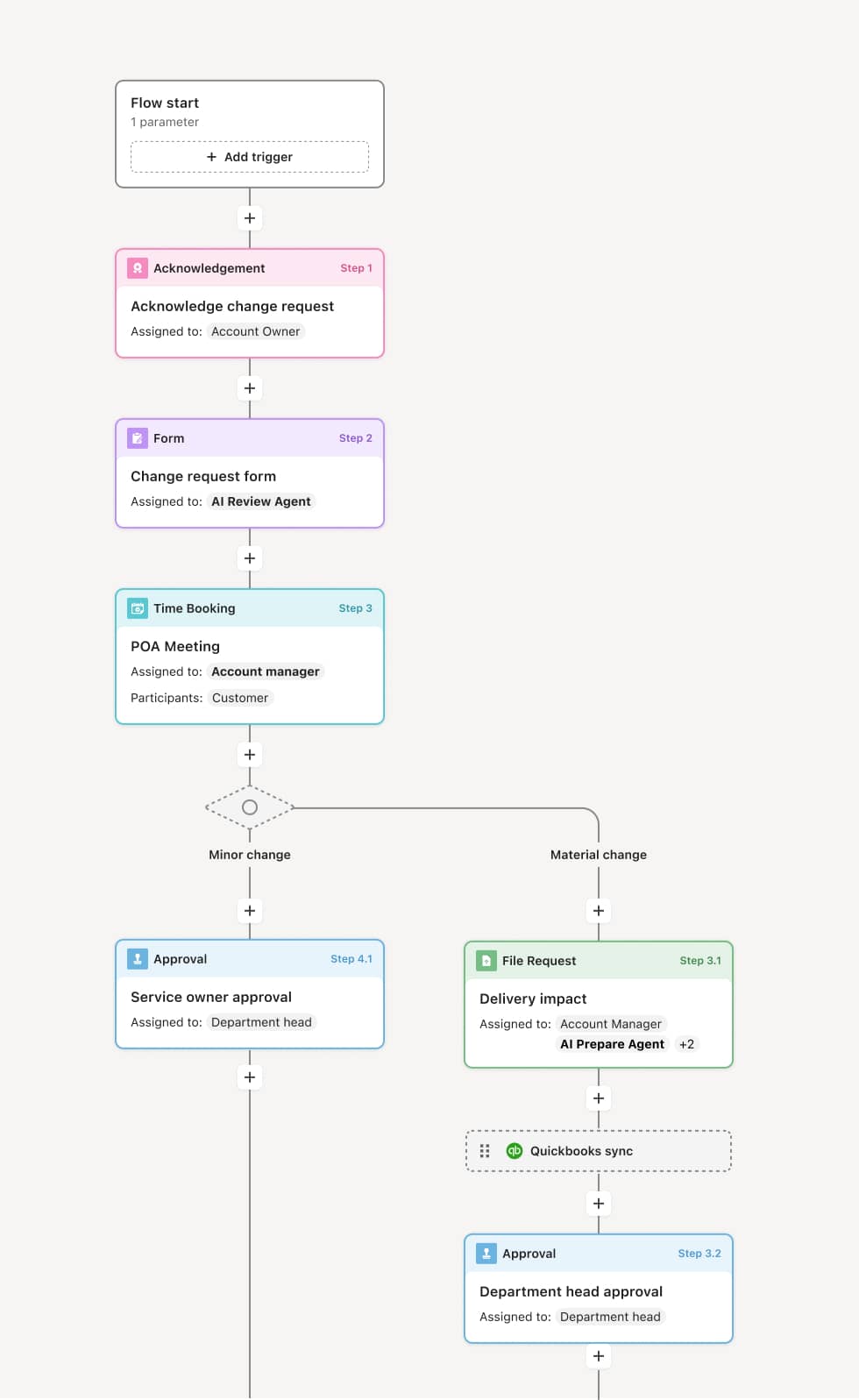
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo’s flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
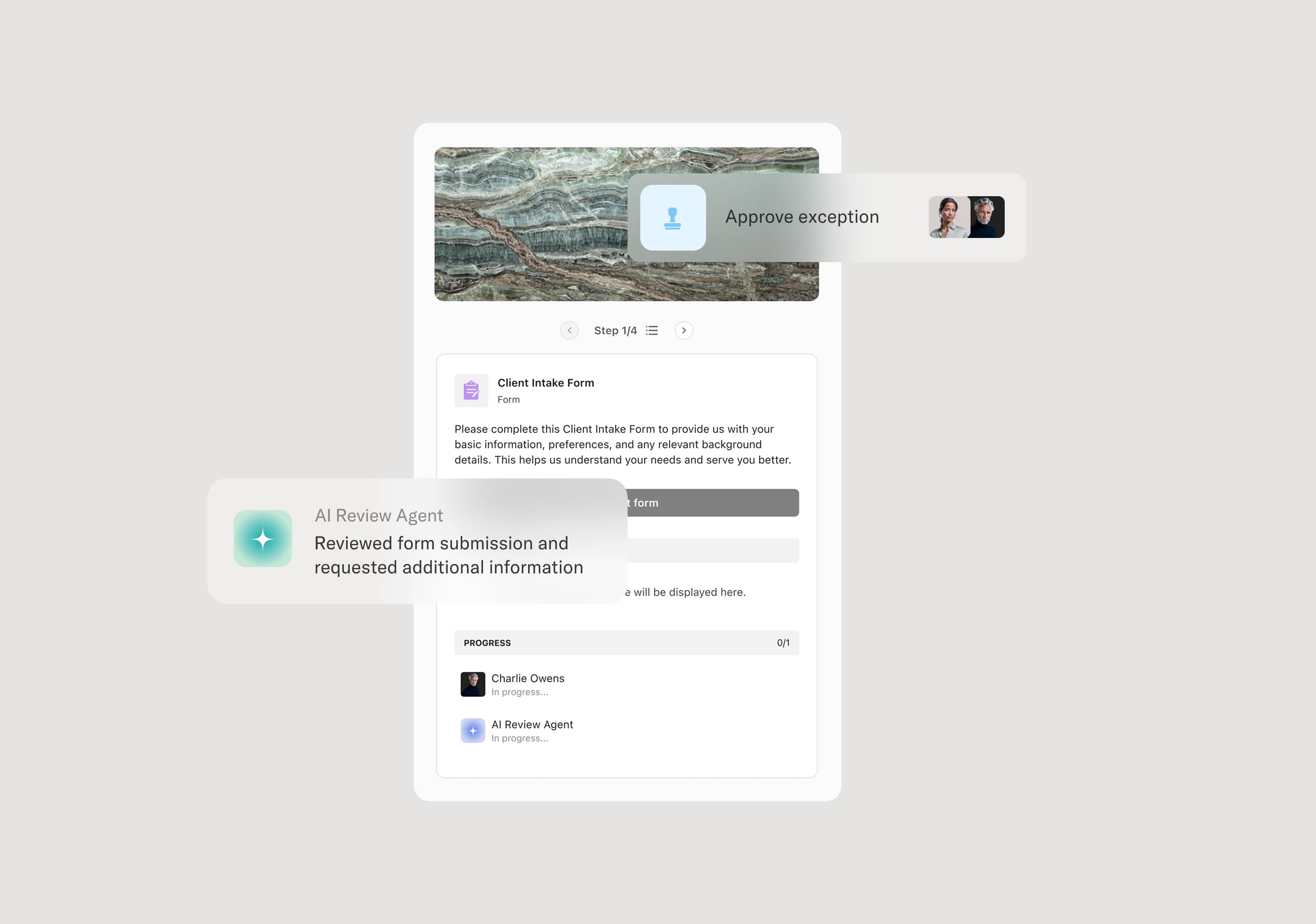
Request submission
The process begins when a requester submits a security approval request describing the proposed change, its business purpose, the systems and data involved, and any known risk factors. An AI Agent can assist by pre-populating the request with relevant system and data classification details and flagging whether the change type historically requires elevated review.
Security risk assessment
The security team evaluates the request against the organization’s risk framework, security policies, and control requirements. The assessment considers data sensitivity, system exposure, integration points, and threat surface. If the change is low-risk and aligns with established controls, it may be approved at this stage. Higher-risk changes are escalated.
IT operations impact review
IT operations assesses the implementation impact of the proposed change, including system dependencies, availability risks, and deployment considerations. This review may proceed in parallel with the security risk assessment. If implementation would introduce significant availability or performance risk, additional safeguards or phased deployment may be recommended.
Compliance assessment
For changes that involve regulated data, cross-border data flows, or third-party access, compliance reviews the request for regulatory alignment. An AI Agent may surface relevant compliance requirements based on the data classification and systems involved.
Approval decision
The request is routed to the appropriate approver based on its risk level. Low and moderate-risk changes may be approved by a security manager. High-risk or policy-exception changes are escalated to the CISO or a security governance board. The approver authorizes the change, authorizes with conditions, requires mitigation actions, or denies the request.
Implementation authorization and closure
Upon approval, the change is authorized for implementation with any specified conditions. Post-implementation, the security team may verify that conditions were met. The complete request, assessment, and approval record is preserved.
This process commonly relies on inputs such as change request details, system architecture documentation, data classification records, security policy references, and vendor security assessments. It may be triggered by a change management request, a new vendor onboarding, a project initiation, or a direct submission from IT or business teams. Connected systems often include ITSM platforms like ServiceNow or Jira Service Management, GRC tools like Archer, and identity management systems for access-related requests.
Key decision points include whether the proposed change falls within established risk tolerance and policy parameters, whether the data and systems involved trigger compliance review requirements, whether implementation risk requires additional safeguards or phased deployment, and at what authority level the change must be approved based on its risk classification.
Vague request descriptions that fail to specify which systems, data, or integrations are affected, requiring security teams to request additional information and delaying review. Over-classified risk levels that route routine changes to senior security leadership unnecessarily, creating bottlenecks. Compliance requirements identified late in the review process because data classification or regulatory triggers were not flagged at submission. Post-approval changes to implementation scope that proceed without returning through the security review process.
Orchestrates security review across requesters, security analysts, IT operations, and compliance in a single structured flow with clear accountability at every stage.
Routes requests based on risk classification and change type so low-risk changes are approved quickly while high-risk items reach the appropriate authority.
AI Agents pre-populate request context by pulling system data, data classification details, and policy references to accelerate the assessment.
Supports parallel security, IT, and compliance reviews so multiple assessment tracks proceed concurrently rather than sequentially.
Connects to ITSM and GRC platforms like ServiceNow, Jira Service Management, and Archer so change data and approval records remain synchronized.
Preserves the complete security approval record including risk assessments, reviewer comments, conditions, and authorization decisions for audit and governance.