API access requester
Engineering reviewer
Security reviewer
Platform owner
Compliance reviewer

API access approval is triggered when developers, applications, partners, or third parties require programmatic access to organizational systems or data. This occurs during application development, partner integrations, vendor onboarding, internal tool creation, and data sharing arrangements. The process applies when API access carries security or compliance implications, when credentials grant access to sensitive data or critical systems, when external parties require programmatic connectivity, or when governance requirements mandate approval before access is provisioned. It is common in technology companies, financial services, healthcare, and any organization exposing APIs internally or externally.
API access approval typically involves requesters such as developers or integration teams who need programmatic access, application or system owners who authorize access to their platforms, IT security teams who evaluate risk and enforce security standards, compliance officers who ensure access aligns with data governance policies, and platform administrators who provision credentials and configure access controls. For partner or vendor integrations, external relationship owners may also participate.
Controlled credential issuance ensures API keys and tokens are granted only after appropriate review, reducing risk of unauthorized access. Clear accountability for access decisions documents who approved access, under what conditions, and for what purpose. Faster developer onboarding results from structured approval paths that eliminate confusion about how to request and receive API access. Reduced security incidents comes from consistent evaluation of access requests against security standards before credentials are issued. Improved compliance posture follows from documented approval processes that demonstrate governance over programmatic access.
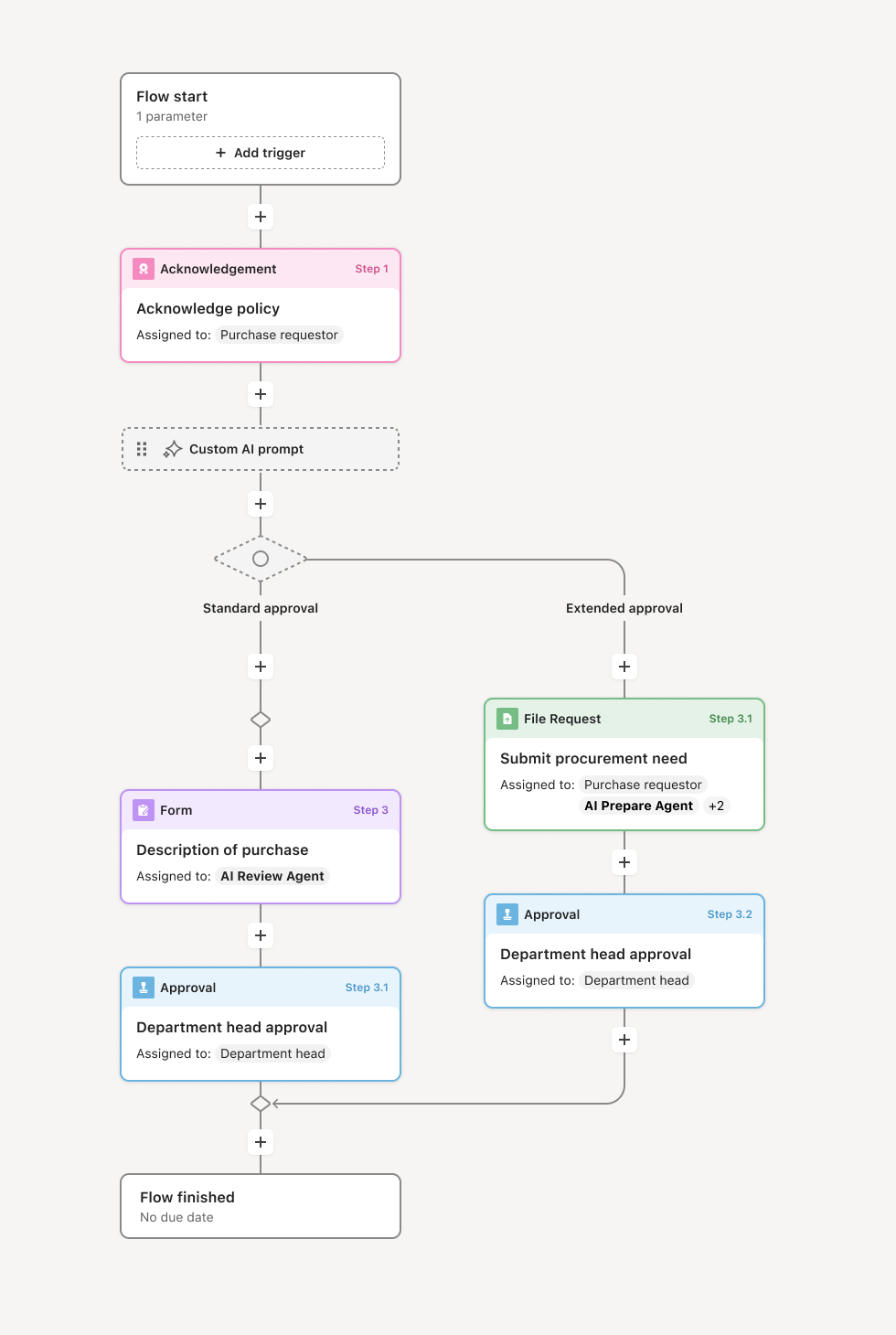
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo's flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Access request submission
The process begins when a requester submits an API access request, specifying the system or service they need to access, the intended use case, the level of access required, and any relevant project or business context. The request includes information about how credentials will be stored and managed. An AI agent may assist by validating request completeness and flagging missing information.
Use case and business justification review
The application or system owner reviews the request to validate the business need and confirm the access level is appropriate for the stated use case. If the use case is unclear or access level seems excessive, the workflow routes back to the requester for clarification. Owners may approve routine access or flag requests requiring additional security review.
Security and compliance evaluation
For access that touches sensitive data, critical systems, or external parties, security and compliance teams evaluate the request. Security reviews the requester's credential management practices, network security posture, and alignment with security policies. Compliance confirms the access aligns with data governance requirements and any applicable regulations. If concerns arise, the workflow routes to address them before proceeding.
Conditional approval paths
Different access types follow different approval paths based on risk level. Internal development access to non-production systems may require only owner approval. Access to production data or customer information may require security sign-off. External partner access may require legal review of data sharing terms. Conditional logic ensures each request follows the appropriate path.
Credential provisioning
Upon approval, the workflow triggers credential provisioning. API keys, tokens, or certificates are generated and delivered securely to the requester. Access parameters such as rate limits, scope restrictions, and expiration dates are configured based on approved terms. The requester acknowledges receipt and agrees to usage terms.
Ongoing access management
The workflow tracks access grants and supports periodic review. Credentials approaching expiration trigger renewal processes. Access no longer needed is revoked through a parallel workflow. The complete history of access grants, modifications, and revocations is retained for audit purposes.
This process commonly relies on inputs such as access request forms, system documentation, security questionnaires, and data classification information. It may be triggered by a developer request, partner onboarding process, or integration project kickoff. Supporting systems often include identity management platforms, API gateways, secrets management tools, and developer portals.
Key decision points include determining whether the use case justifies the requested access level, whether security and compliance review is required based on data sensitivity, whether credential management practices meet organizational standards, and whether access should be time-limited or require periodic renewal.
Access granted without proper security review, exposing sensitive systems to inadequately vetted requesters. Credentials issued with excessive permissions, violating least-privilege principles. No tracking of issued credentials, making it impossible to know what access exists. Credentials never revoked when no longer needed, creating accumulated access risk. Approval process too slow, driving developers to work around controls.
Orchestrates API access approval across requesters, system owners, and security teams in a single coordinated process.
Routes requests through appropriate review paths based on sensitivity and risk using conditional logic that enforces security policies.
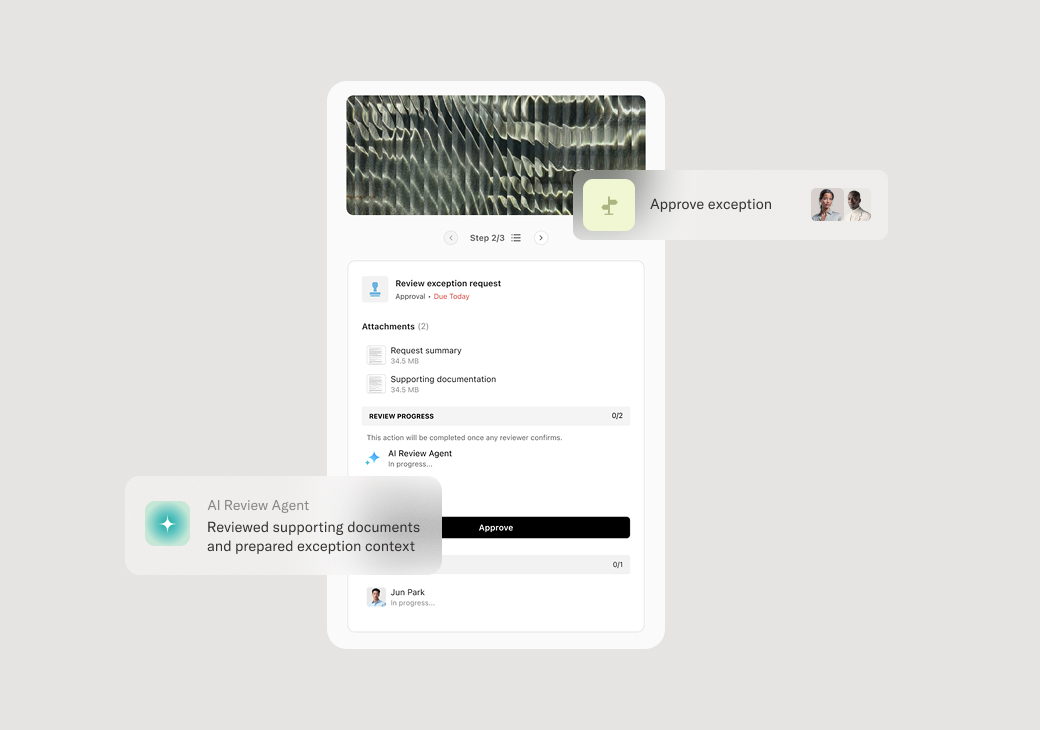
AI agents validate request completeness and flag potential issues before security review begins.
Captures full approval history documenting who authorized access, under what conditions, and for what purpose.
Tracks credential lifecycle including issuance, renewal, and revocation for complete access governance.
Connects to identity management and API gateway systems to trigger provisioning automatically upon approval.