HIPAA privacy officer
HIPAA security officer
Compliance director
IT security manager
Chief information officer
Legal counsel

This process is used on an ongoing basis to maintain the organization’s HIPAA compliance program, including annual risk assessments, policy reviews and updates, workforce training, business associate agreement management, and monitoring of safeguards. It applies when regulatory changes, new systems, organizational growth, or audit findings require updates to the compliance program. It is common when privacy officers, security officers, IT, legal, and department leaders must coordinate across the organization. Ideal for healthcare providers, health plans, clearinghouses, business associates, and any covered entity or business associate under HIPAA.
The HIPAA compliance process typically involves the privacy officer who oversees PHI privacy policies, the security officer who manages technical and physical safeguards, IT and security teams who implement and monitor controls, legal counsel who reviews business associate agreements, compliance coordinators who manage training and audits, and department leaders who ensure workforce compliance.
Demonstrated regulatory compliance through documented risk assessments, policies, training, and monitoring activities that satisfy OCR audit expectations. Reduced breach risk by identifying and addressing vulnerabilities through regular risk assessments and remediation tracking. Current and enforceable policies that reflect the organization’s actual operations, systems, and regulatory requirements. Trained workforce with documented evidence of HIPAA training completion across all workforce members. Managed business associate risk through systematic tracking of BAA execution and compliance obligations.
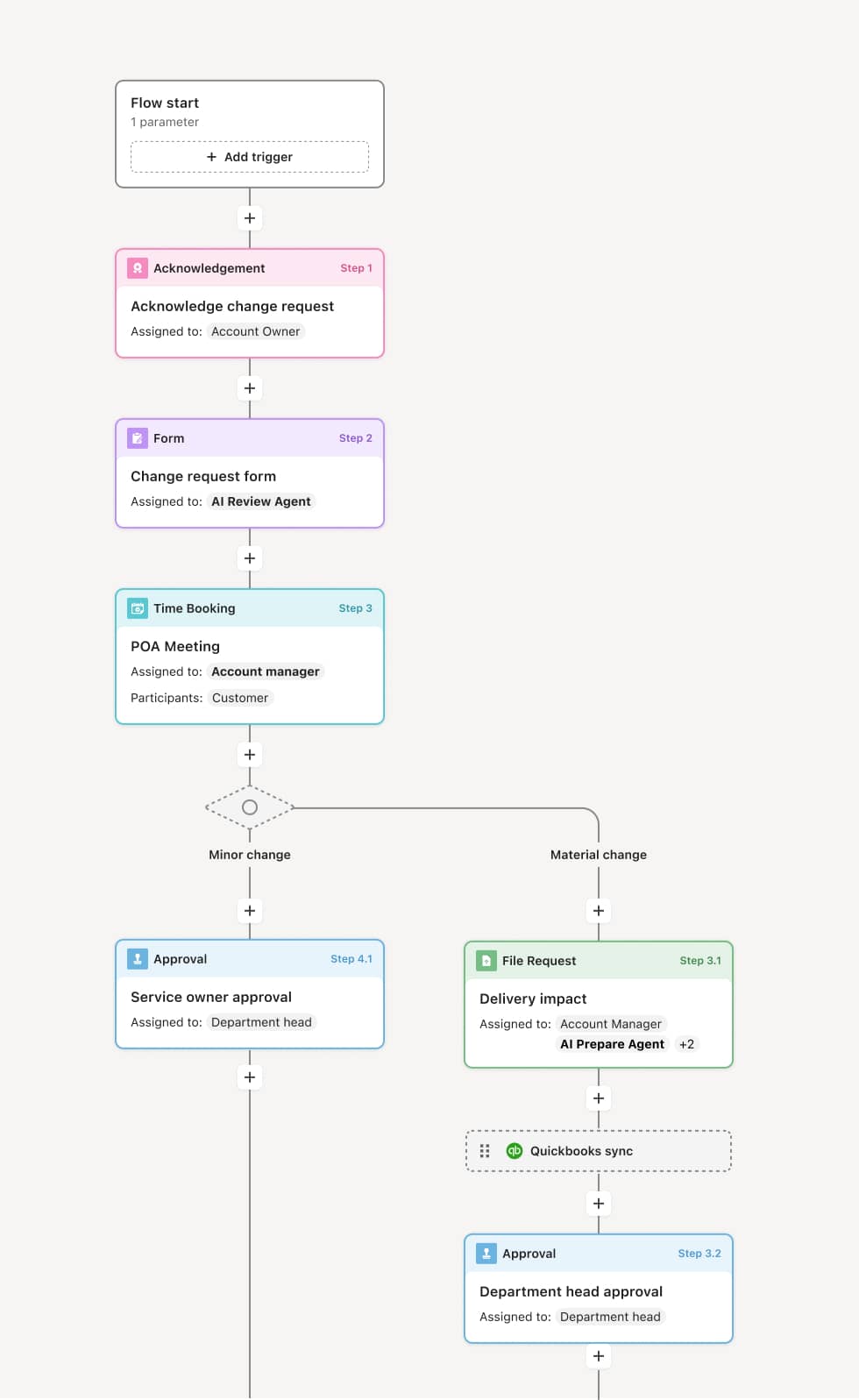
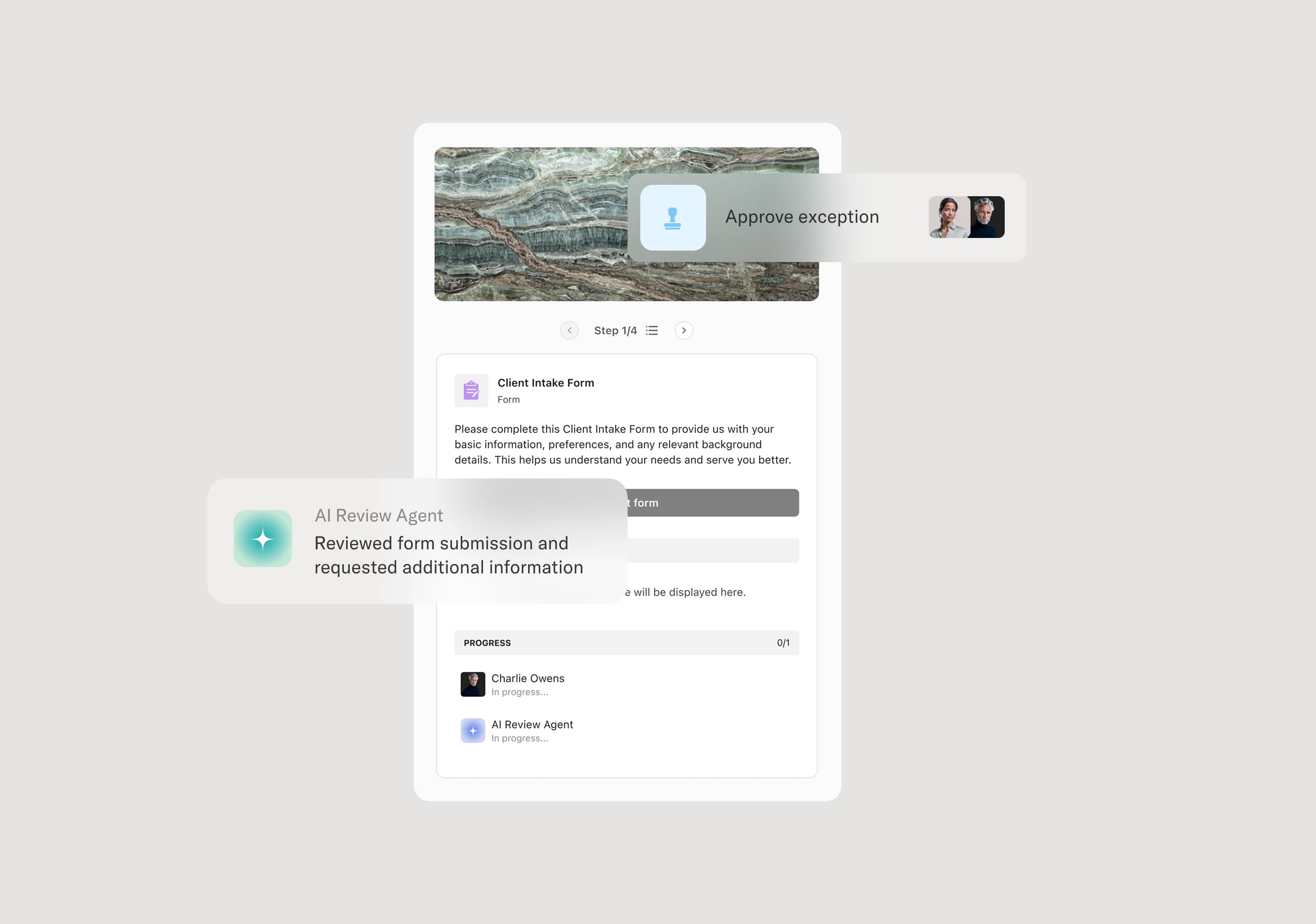
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo’s flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Risk assessment and analysis
The process includes conducting periodic security risk assessments as required by the HIPAA Security Rule. The security officer leads the assessment, evaluating threats and vulnerabilities to electronic PHI across systems, facilities, and workflows. The assessment produces a risk register with identified risks, likelihood, impact, and recommended mitigations. An AI Agent can assist by compiling system inventories, prior assessment findings, and known vulnerability data to prepare the assessment team.
Policy development and review
Privacy and security policies are developed, reviewed, and updated on an annual cycle or when triggered by regulatory changes, system changes, or incident findings. Policies cover access controls, encryption, breach notification, minimum necessary, workforce sanctions, and business associate management. Each policy is reviewed by the responsible officer and approved by compliance leadership.
Workforce training and attestation
All workforce members receive HIPAA training upon hire and at defined intervals thereafter. Training covers privacy and security obligations, PHI handling, breach reporting, and sanctions. Completion and attestation are documented for each individual. An AI Agent may track training completion status across the organization and flag overdue individuals.
Business associate agreement management
The organization maintains a registry of business associates and ensures that each has a current, executed business associate agreement. BAAs are reviewed when vendor relationships change, contracts are renewed, or regulatory requirements are updated. An AI Agent may track BAA expiration dates and flag agreements due for renewal.
Ongoing monitoring and remediation
The compliance team monitors safeguards through periodic audits, access log reviews, incident tracking, and vulnerability assessments. Identified deficiencies are logged in the risk register and tracked through remediation to completion. The security officer verifies that remediation actions are implemented and effective.
Compliance documentation and audit readiness
All compliance activities — risk assessments, policies, training records, BAA documentation, incident logs, and remediation tracking — are maintained in a centralized compliance record that supports OCR investigation, external audit, and organizational governance review.
This process commonly relies on inputs such as the risk assessment, system and asset inventories, policy documents, training records, BAA agreements, audit logs, and incident reports. It may be triggered by the annual compliance cycle, a regulatory change, an incident, or an audit finding. Connected systems often include compliance management platforms, learning management systems for training tracking, GRC (governance, risk, and compliance) platforms, and IT security tools for vulnerability and access monitoring.
Key decision points include which risks identified in the assessment require immediate remediation versus those that can be mitigated through acceptable controls, whether policies need to be updated based on regulatory changes or organizational changes, whether workforce training programs address current threats and requirements, and whether business associate agreements are current and adequate for the organization’s vendor relationships.
Risk assessments not conducted or not documented at the required frequency, creating a critical compliance gap. Policies outdated because they have not been reviewed after system changes, regulatory updates, or organizational growth. Training records incomplete for a significant portion of the workforce, making it impossible to demonstrate compliance during an audit. BAA inventory not maintained, leaving the organization unable to confirm that all business associates are under current agreements. Remediation actions not tracked to completion, allowing identified vulnerabilities to persist.
Orchestrates the ongoing HIPAA compliance program across privacy officers, security officers, IT, legal, and department leaders in a coordinated workflow that keeps all compliance activities on schedule.
Manages the risk assessment cycle from planning through remediation tracking, ensuring assessments are completed and documented on time.
AI Agents track training completion, BAA expiration dates, and policy review schedules across the organization, flagging overdue items before they become compliance gaps.
Coordinates policy review and approval within the workflow so updates are reviewed, approved, and distributed with documented accountability.
Connects to compliance management and GRC platforms so risk registers, audit logs, and remediation activities are synchronized with the overall compliance record.
Preserves the complete compliance documentation including risk assessments, policies, training records, BAAs, incident logs, and remediation evidence for OCR audit readiness.