Information security manager
Chief information security officer
Risk manager
IT operations lead
Compliance officer
Business unit director

This process is used when a business unit, project, or system requires a deviation from an established security policy — such as a control bypass, a non-standard configuration, a temporary access elevation, or a policy waiver — and that deviation must be formally reviewed and authorized. It applies when the exception carries risk that must be assessed, documented, and accepted at an appropriate level of authority. It is common when operational urgency, legacy system constraints, or third-party requirements create scenarios where full policy compliance is not immediately feasible. Ideal for technology, financial services, healthcare, government, and any organization with formal information security governance frameworks.
The security exception approval process typically involves the requester who identifies the need for an exception and provides the business justification, security analysts who assess the associated risk and impact, risk owners who accept accountability for the exposure, compliance officers who evaluate regulatory implications, and the CISO or a security governance board who authorize the exception with documented conditions and time limits.
Governed exception handling so deviations from policy are evaluated, documented, and authorized rather than ignored or handled informally. Time-bound risk acceptance with clear expiration dates and conditions that prevent exceptions from becoming permanent unmanaged exposures. Documented accountability where every exception has an identified risk owner, approval authority, and recorded rationale. Reduced shadow risk by providing a structured path for exceptions, discouraging teams from bypassing security policy without review. Stronger audit readiness because exception decisions, risk assessments, and conditions are preserved as part of the governance record.
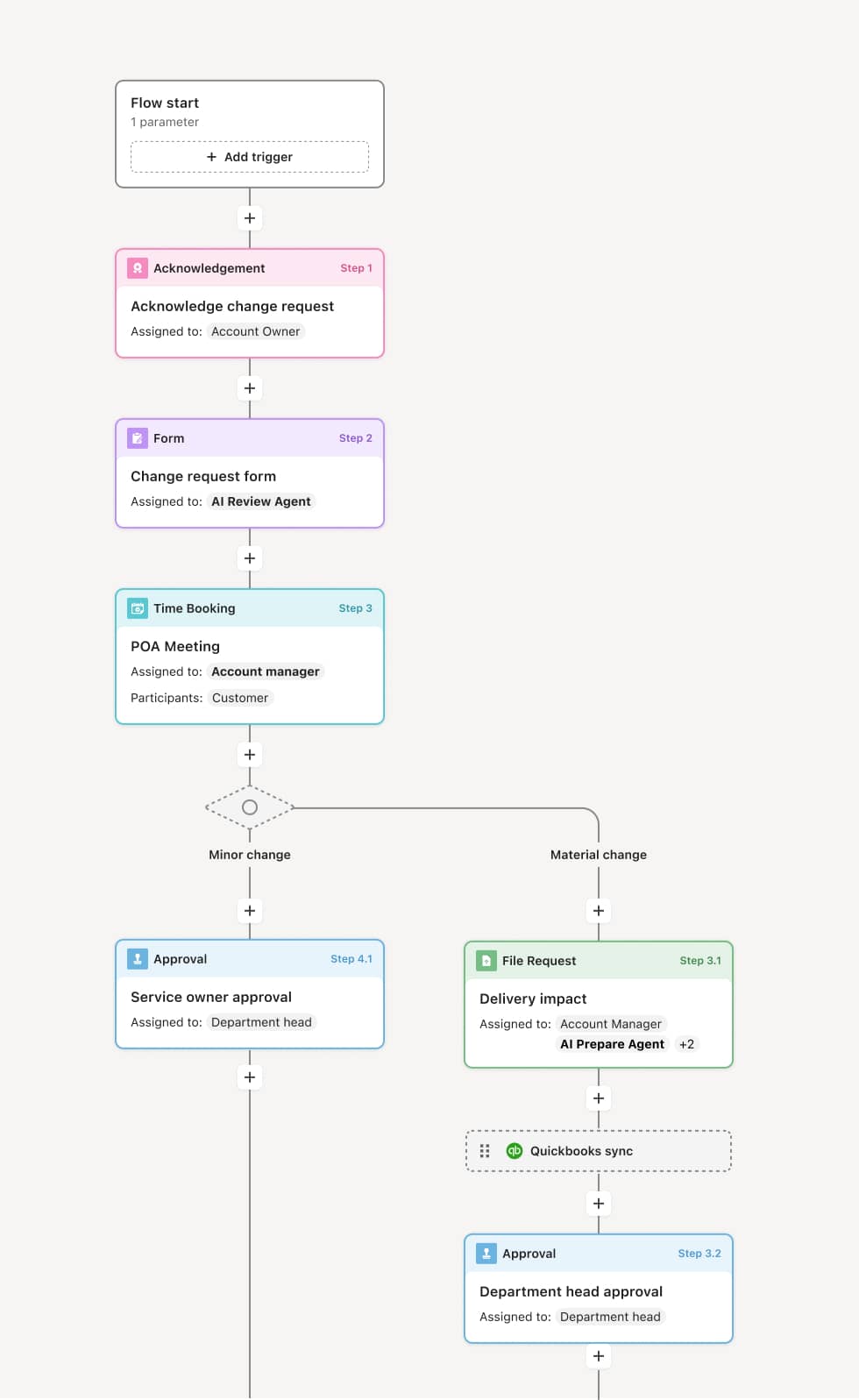
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo’s flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
Exception request and business justification
The process begins when a requester identifies that a security policy cannot be fully met and submits an exception request. The submission includes the specific policy being deviated from, the business reason, the systems and data affected, and the proposed duration. An AI Agent can assist by pulling the relevant policy text and identifying prior exceptions granted for the same policy or system.
Security risk assessment
The security team evaluates the risk introduced by the exception, considering the sensitivity of the data and systems involved, the threat exposure created, and the availability of compensating controls. The risk assessment produces a severity rating that determines the approval path. If compensating controls can reduce the risk to an acceptable level, those are documented as conditions.
Compliance and regulatory review
If the exception involves regulated data, compliance-critical systems, or controls required by frameworks such as SOC 2, HIPAA, PCI-DSS, or ISO 27001, the exception is routed to a compliance officer for additional assessment. An AI Agent may flag which regulatory frameworks are implicated based on the systems and data involved.
Risk owner acknowledgment
The designated risk owner — typically the business unit leader or system owner — formally acknowledges the residual risk associated with the exception and accepts accountability for the exposure during the exception period.
Approval decision
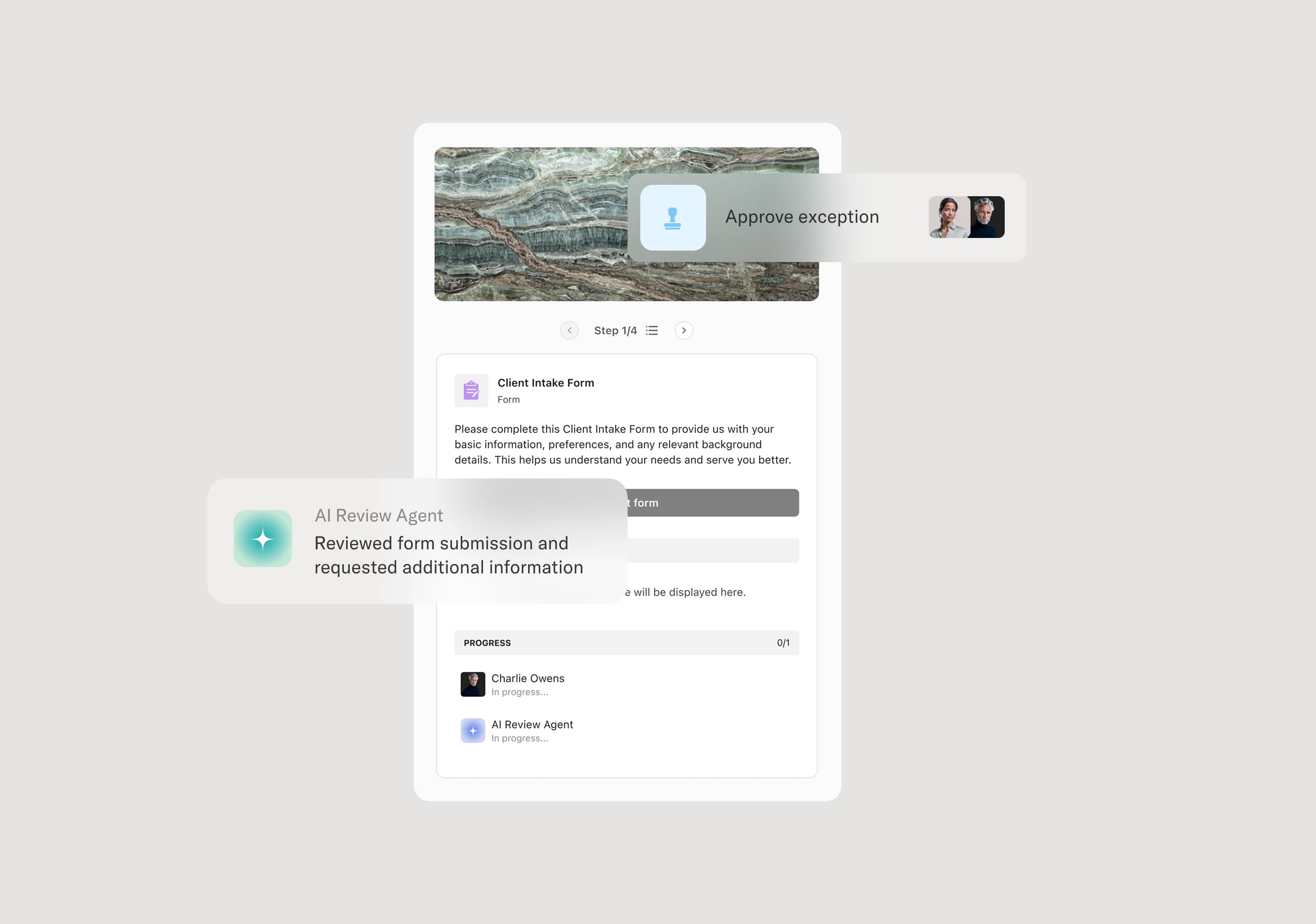
The exception is routed to the appropriate authority based on its risk level. Moderate-risk exceptions may be approved by the security manager with conditions. High-risk or compliance-affecting exceptions are escalated to the CISO or a security governance board. The approver authorizes the exception with conditions and an expiration date, requires additional compensating controls, or denies the request.
Monitoring and expiration
The approved exception is tracked with its conditions, compensating controls, and expiration date. As the expiration approaches, the process triggers a review to determine whether the exception should be renewed, the underlying issue resolved, or the exception revoked. An AI Agent can monitor the expiration timeline and notify stakeholders in advance.
Closure and governance record
Upon resolution — whether by remediation, renewal, or revocation — the exception record is closed with a documented outcome. The full exception history, including risk assessment, approvals, conditions, and monitoring notes, is preserved.
This process commonly relies on inputs such as exception request details, the specific security policy reference, risk assessment documentation, compensating control proposals, and business justification. It may be triggered by a project requirement, an audit finding, a system migration constraint, or a third-party integration need. Connected systems often include GRC platforms like Archer or ServiceNow, ITSM tools for change management context, and compliance tracking systems for regulatory framework alignment.
Key decision points include whether the exception risk can be mitigated by compensating controls to an acceptable level, whether the exception involves regulated data or compliance-critical controls requiring additional review, at what authority level the exception must be approved based on its risk severity, and whether the exception should be renewed or revoked upon expiration.
Exceptions requested without adequate business justification, forcing security teams to seek additional context and delaying assessment. Compensating controls not clearly defined, leaving residual risk unmanaged during the exception period. Exception expiration dates missed because no monitoring or renewal process is in place, allowing temporary exceptions to become permanent exposures. Risk owner accountability unclear, so the business unit accepting the risk is not formally identified or committed. Fragmented exception records when risk assessments, approvals, and conditions are tracked in separate systems, undermining audit readiness.
Orchestrates the full exception lifecycle from request through monitoring and expiration across requesters, security teams, risk owners, compliance, and leadership.
Routes exceptions based on risk severity so moderate exceptions are handled efficiently while high-risk or compliance-affecting items reach the right governance authority.
AI Agents surface relevant policy references and prior exception history at submission, helping requesters provide adequate context and security teams assess risk faster.
Tracks compensating controls and expiration dates within the workflow so conditions are monitored and renewal or remediation is triggered before exceptions lapse.
Connects to GRC and ITSM platforms like Archer, ServiceNow, and compliance tracking tools so exception records and governance data stay synchronized.
Preserves a complete exception governance record including every request, risk assessment, approval condition, and resolution outcome for audit and regulatory review.