Third-party risk manager
Procurement director
Compliance officer
Vendor management lead
Legal counsel
Operations director

This process is used when the organization plans to engage a new third party — or renew an existing relationship — and must evaluate whether the third party meets required standards for data security, regulatory compliance, financial stability, and operational capability. It applies when third-party risk assessments, due diligence reviews, or compliance checks are required by organizational policy, regulatory mandate, or contractual obligation. It is common when procurement, compliance, legal, information security, and the sponsoring business unit must coordinate their evaluations. Ideal for financial services, healthcare, technology, government, and any regulated or enterprise environment with formal third-party risk management programs.
The third party approval process typically involves the business owner or sponsor who requests the engagement, procurement or vendor management who coordinates the evaluation, compliance officers who assess regulatory and policy alignment, information security who evaluates data and system risk, legal who reviews contractual terms, and a third-party risk committee or senior approver who authorizes the engagement based on the aggregate assessment.
Reduced third-party risk by ensuring every external engagement is evaluated against consistent security, compliance, and capability standards. Faster third-party onboarding by routing evaluations to the right teams in parallel based on the engagement’s risk profile. Consistent due diligence across all third parties regardless of sponsoring department, preventing gaps in risk coverage. Documented authorization so every approved third party has a recorded risk assessment, conditions, and accountable approver. Regulatory compliance because third-party evaluations satisfy requirements from frameworks such as OCC guidance, GDPR, HIPAA, and SOC 2.
Your version of this process may vary based on roles, systems, data, and approval paths. Moxo’s flow builder can be configured with AI agents, conditional branching, dynamic data references, and sophisticated logic to match how your organization runs this workflow. The steps below illustrate one example.
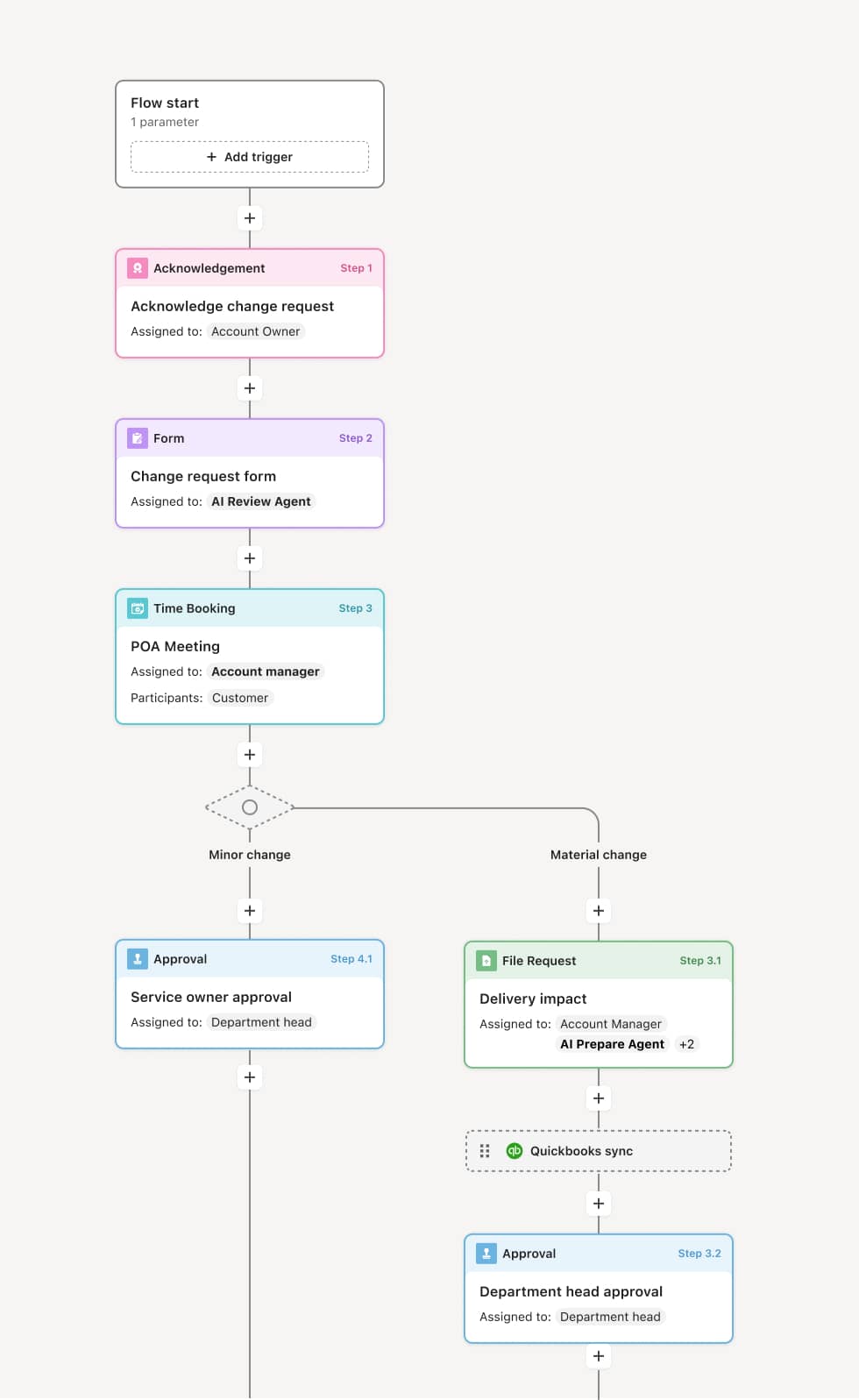
Engagement request and risk profiling
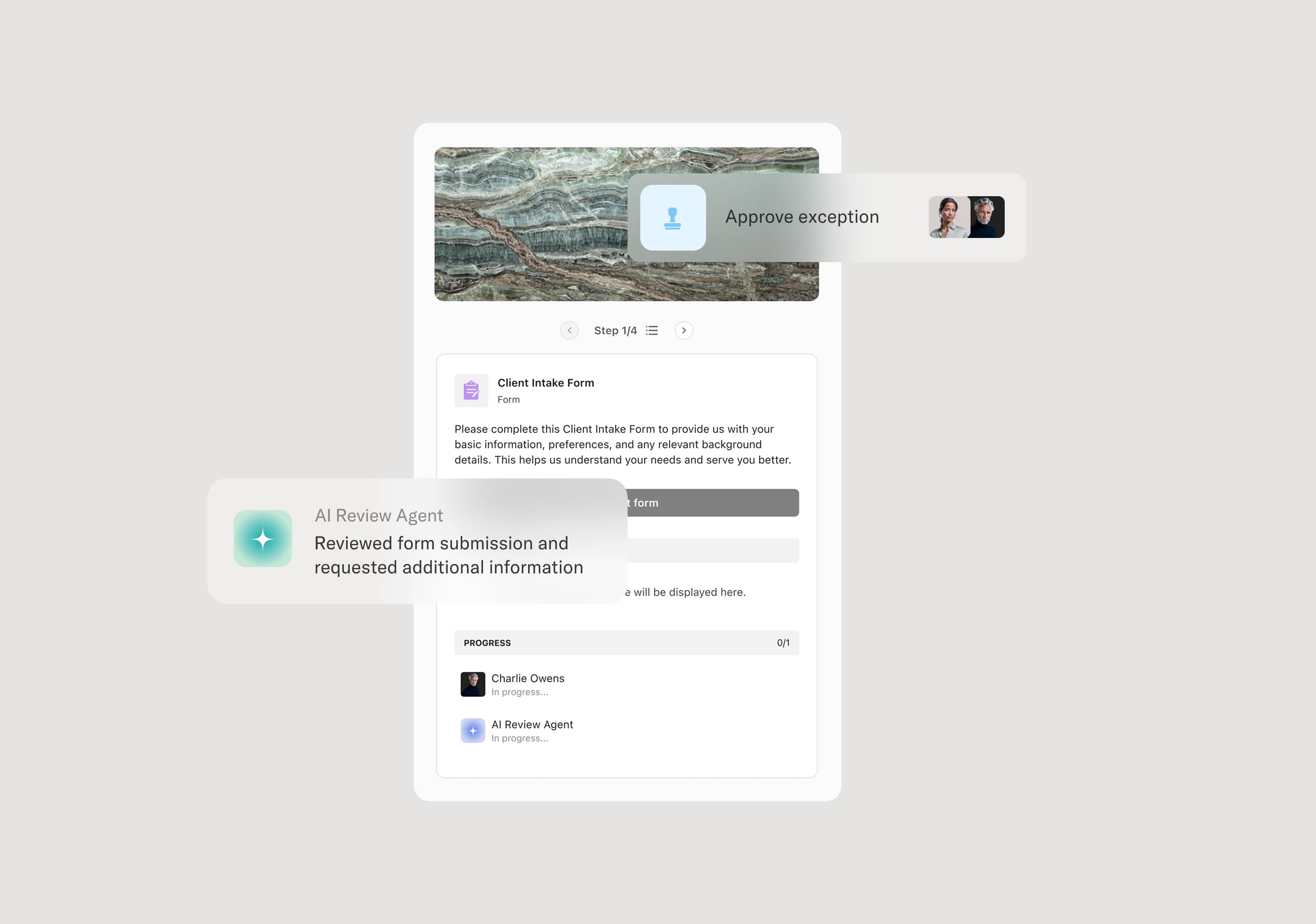
The process begins when a business owner or sponsor submits a request to engage a new third party. The submission includes the nature of the engagement, data access requirements, systems involved, and business justification. An AI Agent can assist by classifying the engagement’s risk tier based on data sensitivity, regulatory context, and engagement scope, which determines the depth of evaluation required.
Third-party information collection
The third party is invited to provide required documentation, including security questionnaires, compliance certifications, financial statements, insurance certificates, and references. An AI Agent may validate the completeness of the submission and flag missing items before the evaluation begins.
Risk and compliance evaluation
Multiple evaluation tracks proceed based on the risk tier. Information security assesses data handling, access controls, and cybersecurity posture. Compliance reviews regulatory alignment, certifications, and policy adherence. Finance evaluates financial stability. For high-risk engagements, all tracks are required. For lower-risk engagements, a streamlined assessment may apply. An AI Agent may cross-reference the third party’s certifications against the required standards for the engagement type.
Legal and contractual review
Legal reviews the proposed contractual terms, including data processing agreements, liability provisions, indemnification, and termination rights. If terms require negotiation, the process branches to include the third party in the discussion.
Approval decision
The aggregate evaluation is routed to the appropriate approver — a third-party risk committee, procurement director, or senior business leader depending on the risk tier. The approver reviews the complete assessment and authorizes the engagement, authorizes with conditions, or declines.
Activation and ongoing monitoring
Upon approval, the third party is activated in procurement and vendor management systems. The engagement enters the organization’s ongoing monitoring cycle for periodic reassessment. The complete evaluation record is preserved for audit and regulatory purposes.
This process commonly relies on inputs such as the engagement request, third-party questionnaires, security assessments, compliance certifications, financial data, and contractual documents. It may be triggered by a new engagement request, a contract renewal, or a regulatory requirement. Connected systems often include third-party risk management platforms like OneTrust, Prevalent, or ProcessUnity, procurement systems like SAP Ariba or Coupa, and GRC platforms like Archer or ServiceNow.
Key decision points include the initial risk classification that determines the evaluation scope, whether the third party’s security, compliance, and financial profiles meet minimum requirements, whether contractual terms adequately protect the organization, and whether the aggregate risk profile warrants full approval, conditional approval, or rejection.
Incomplete third-party submissions that stall the evaluation because critical documentation like security questionnaires or financial statements is missing. Risk tier misclassification that results in insufficient due diligence for high-risk engagements or excessive process for low-risk ones. Sequential evaluations across security, compliance, and finance that extend the timeline beyond business expectations. Conditional approvals not tracked, allowing third parties to operate without completing required remediation actions. Engagement data fragmented across procurement, compliance, and legal systems, making periodic reassessment and audit preparation difficult.
Orchestrates third-party evaluation across procurement, compliance, security, legal, and business sponsors in a single flow that engages the third party directly for documentation and communication.
Routes evaluations based on risk tier so high-risk engagements receive comprehensive assessment while lower-risk ones follow a streamlined path.
AI Agents validate third-party submissions at intake, flagging missing questionnaires, certifications, or financial data before evaluation begins.
Supports parallel evaluation tracks so security, compliance, and financial assessments proceed concurrently, reducing total qualification time.
Engages third parties directly within the workflow so they can submit documentation, respond to questions, and participate in contract discussions in context.
Preserves the complete third-party evaluation record including all submissions, assessments, conditions, and approval decisions for audit, regulatory compliance, and periodic reassessment.